Social Engineering 201: How the User Protection Suite Safeguards Organizations
In Social Engineering 101, we shared the story of John, the well-meaning employee who fell victim to a phishing attack. In this scenario, John was tricked into resetting his password by a bad actor pretending to be the IT team, which gave away access to his account. In that blog, we also discussed the many ways Duo protects John, from strong authentication methods to pairing authentication with device trust policies.
But what if the email never reached John, or the phishing link was blocked? That’s why most organizations do not rely on a single security solution but layer defenses around users and sensitive resources to ensure there isn’t a single point of failure. However, the disparate security solutions meant to protect against particular threats can lead to visibility and administration challenges for organizations.
That’s why Cisco protects users from the top attack vectors targeting organizations with the User Protection Suite, which includes Duo. The User Protection Suite defends all users, devices and access to applications to reduce gaps in the attack surface.
Now, let's rethink the story of John when he is protected by the suite.
In this new story, let's assume that email protection was not in place and the malicious email made it to John. When he clicked on the bad link, Cisco Secure Access would step in and block the user from accessing the malicious destination. Cisco sees 1 million malicious domains every hour, and all that data means we have a good idea when a website should be blocked. In this new scenario, we know John could only click the link on his managed laptop because Duo’s Trusted Endpoints would block email access on unknown or unmanaged devices.
We’ve now seen John’s credentials protected by Duo and his access protected by Secure Access. But now let’s consider if John never received the attacker’s email because Email Threat Defense recognized signs of malicious intent: there was an urgent request, from an unknown sender, with a malicious link. Email Threat Defense uses multiple AI detection engines to determine the difference between true threats and false positives. It would block the email from reaching the end user and quarantine the link to provide the organization’s administrators with the context to better understand the nature of the threats targeting their organization.
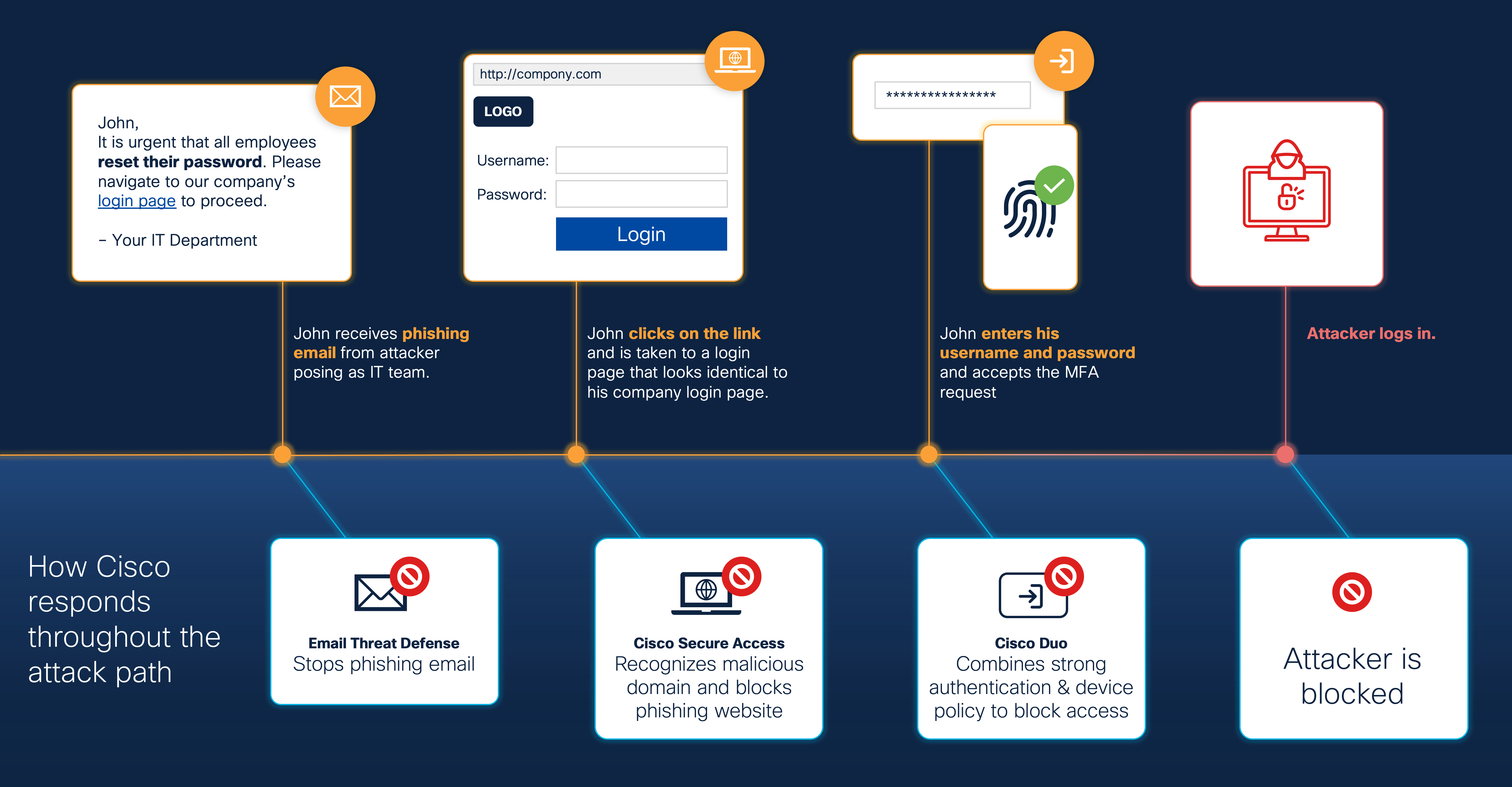
When protecting users against threats, we can never assume there is one silver bullet or singular solution. Attackers are constantly finding new ways to target users and get access to an organization’s resources and data. This is not a new story. However, when Cisco security solutions bring email, web, endpoint and authentication to work together to layer the defenses around the user, that makes our users, and organizations, safer.
To learn more about how the User Protection Suite can protect your organization today, see the Cisco User Protection Suite webpage and connect with an expert today.

