Contents
Add two-factor authentication and flexible security policies to your Red Hat OpenShift logins with Duo Single Sign-On. Our cloud-hosted OpenID identity provider offers inline user enrollment, self-service device management, and support for a variety of authentication methods — such as passkeys and security keys, Duo Push, or Verified Duo Push — in the Universal Prompt.
About Duo Single Sign-On
Duo Single Sign-On is our cloud-hosted SSO product which layers Duo's strong authentication and flexible policy engine on top of Red Hat OpenShift logins using the Security Assertion Markup Language (SAML) 2.0 or OpenID Connect (OIDC) authentication standards. Duo Single Sign-On acts as an OpenID provider (OP), authenticating your users using existing on-premises Active Directory (AD) or any SAML 2.0 IdP and prompting for two-factor authentication before permitting access to Red Hat OpenShift.
Duo Single Sign-On is available in Duo Premier, Duo Advantage, and Duo Essentials plans, which also include the ability to define policies that enforce unique controls for each individual SSO application. For example, you can require that Salesforce users complete two-factor authentication at every login, but only once every seven days when accessing Red Hat OpenShift. Duo checks the user, device, and network against an application's policy before allowing access to the application.
Configure Single Sign-On
Before configuring Red Hat OpenShift with Duo SSO using OpenID Connect (OIDC) authentication you'll first need to enable Duo Single Sign-On for your Duo account and configure a working authentication source.
Once you have your SSO authentication source working, continue to the next step of creating the Red Hat OpenShift application in Duo.
When configuring an application to be protected with Duo Single Sign-On you'll need to send attributes from Duo Single Sign-On to the application. Active Directory will work with no additional setup, but if you used a SAML idenity provider as your authentication source please verify that you configured it to send the correct SAML attributes.
Below you can see the default bridge attributes that automatically map certain attributes from your authentication source.
| Bridge Attribute | Active Directory | SAML IdP |
|---|---|---|
<Username> |
sAMAccountName | Username |
<Email Address> |
||
<Display Name> |
displayName | DisplayName |
<First Name> |
givenName | FirstName |
<Last Name> |
sn | LastName |
Create the Red Hat OpenShift Application in Duo
-
Log in to the Duo Admin Panel and navigate to Applications → Protect an Application.
-
Locate the entry for Red Hat OpenShift with a protection type of "2FA with SSO hosted by Duo (Single Sign-On)" in the applications list. Click Protect to the far-right to start configuring Red Hat OpenShift. See Protecting Applications for more information about protecting applications with Duo and additional application options. You'll need the information on the Red Hat OpenShift page under Metadata later.
-
No users can log in to new applications until you grant access. Update the User access setting to grant access to this application to users in selected Duo groups, or to all users. Learn more about user access to applications. If you do not change this setting now, be sure to update it so that your test user has access before you test your setup.
-
The Metadata section contains OpenID provider information about Duo Single Sign-On you will provide to Red Hat OpenShift at a later configuration step.
-
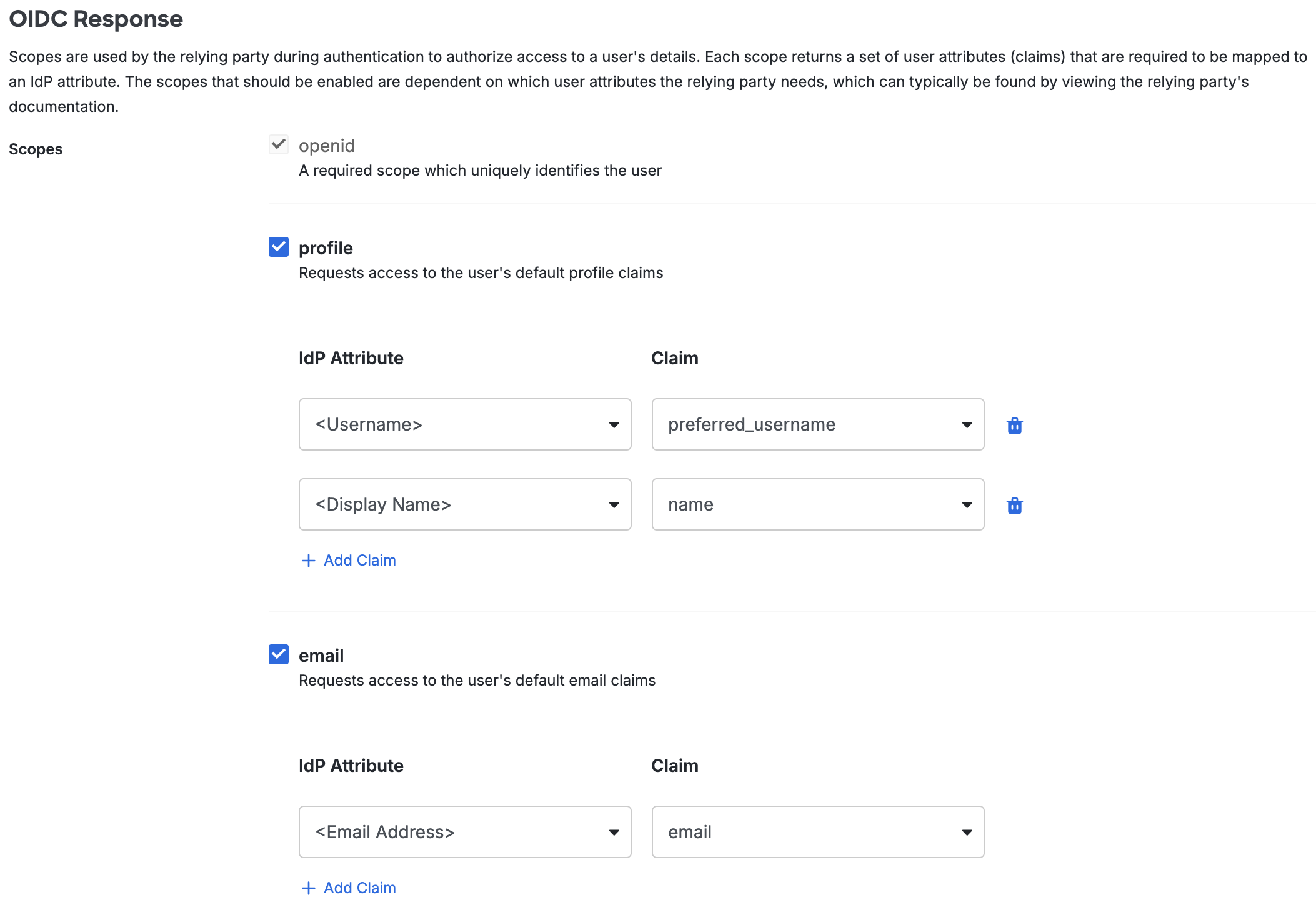
Scopes are used by Red Hat OpenShift during authentication to authorize access to a user's details. Each scope returns a set of user attributes (claims) that must be mapped to IdP attributes. When an application sends an OIDC request to Duo SSO, the response sends only the claims from the requested scopes.
We've automatically enabled the following scopes and mapped the listed attributes. You can change the attribute sent from your authentication source by modifying the IdP Attribute name related to each claim:
-
Profile Scope:
IdP Attribute Claim <Username> preferred_username <Display Name> name -
Email Scope:
IdP Attribute Claim <Email Address> email
-
-
You can adjust additional settings for your new SSO application at this time — like changing the application's name from the default value, enabling self-service, or assigning a group policy.
-
Keep the Duo Admin Panel tab open. You will come back to it later.
Duo Universal Prompt
The Duo Universal Prompt provides a simplified and accessible Duo login experience for web-based applications, offering a redesigned visual interface with security and usability enhancements.
| Universal Prompt | Traditional Prompt |
 |
 |
The Duo Red Hat OpenShift application supports the Universal Prompt by default, so there's no additional action required on your part to start using the newest authentication experience.
Activate Universal Prompt
Activation of the Universal Prompt is a per-application change. Activating it for one application does not change the login experience for your other Duo applications. Universal Prompt is already activated for new Red Hat OpenShift applications at creation.
The "Universal Prompt" area of the application details page shows that this application's status is "Activation complete", with these activation control options:
- Show traditional prompt: Your users experience Duo's traditional prompt via redirect when logging in to this application.
- Show new Universal Prompt: (Default) Your users experience the Universal Prompt via redirect when logging in to this application.
The application's Universal Prompt status shows "Activation complete" both here and on the Universal Prompt Update Progress report.
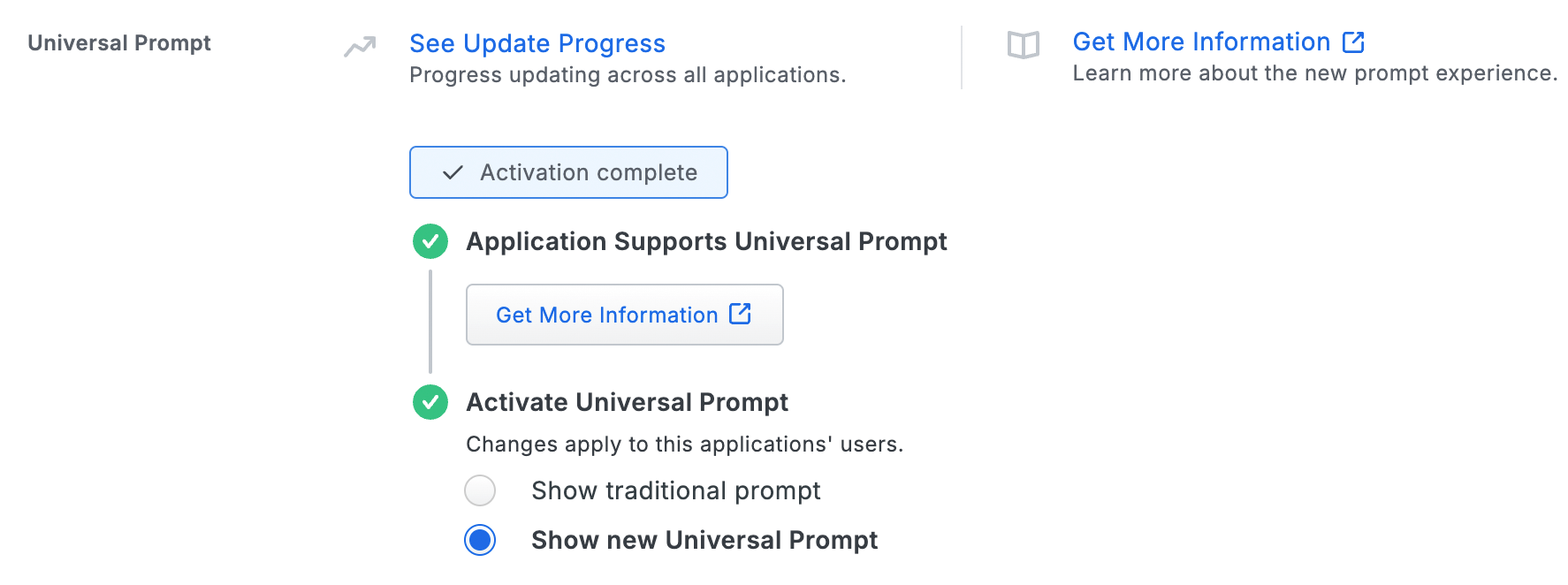
For the time being, you may change this setting to Show traditional prompt to use the legacy experience. Keep in mind that support for the traditional Duo prompt ended for the majority of applications in March 2024. This option will be removed in the future.
Universal Update Progress
Click the See Update Progress link to view the Universal Prompt Update Progress report. This report shows the update availability and migration progress for all your Duo applications. You can also activate the new prompt experience for multiple supported applications from the report page instead of visiting the individual details pages for each application.
Configure Red Hat OpenShift
-
Log into your Red Hat OpenShift console as an administrator.
-
In the left menu sidebar, navigate to Administration → Cluster Settings. The "Cluster Settings" page opens.
-
Click the Configuration tab.
-
In the "Configuration resource" column, click OAuth.
-
Make sure the Details tab is selected.
-
In the "Identity providers" section, click the Add drop-down menu and select OpenID Connect. The "Add Identity Provider: OpenID Connect" page opens.
-
Enter a unique name for your identity provider into the Name field. Make note of your identity provider name. You will need it later.
-
Return to the Duo Admin Panel. Under "Metadata", copy the items listed below and paste them into their respective fields in Red Hat OpenShift:
-
Copy the Client ID and paste it into the Red Hat OpenShift Client ID field.
-
Copy the Client Secret and paste it into the Red Hat OpenShift Client secret field.
-
Copy the Issuer URL and paste it into the Red Hat OpenShift Issuer URL field.
-
-
In Red Hat OpenShift, scroll down to the "More options" section.
-
Click inside the empty field under "Extra scopes" and type email.
-
Click Add more to add another empty field and type profile.
-
At the bottom of the page, click Add.
-
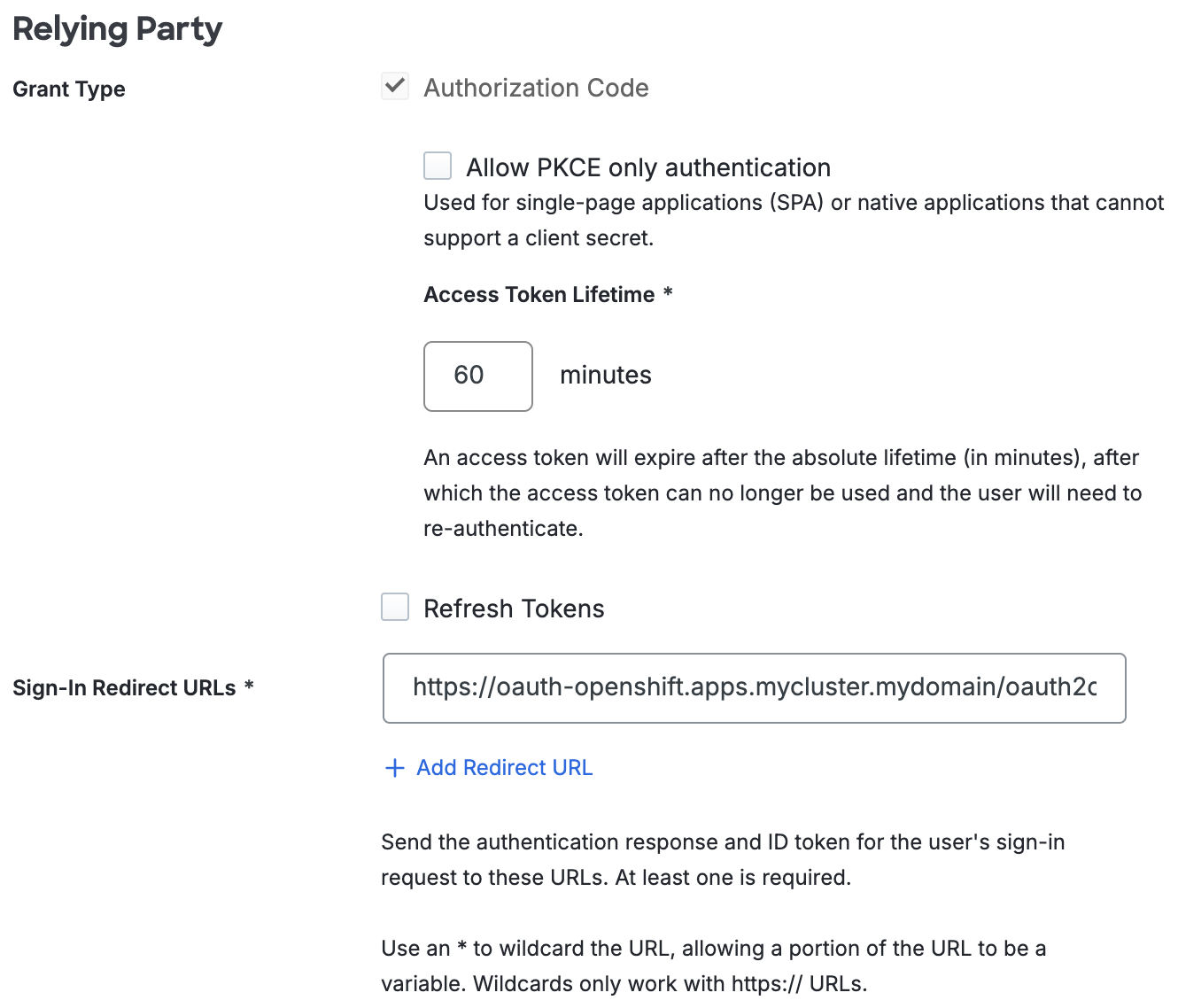
Return to the Duo Admin Panel. Under "Relying Party", type https://oauth-openshift.apps.<cluster_name>.<cluster_domain>/oauth2callback/<idp_provider_name> into the Sign-In Redirect URLs field.
Replace <cluster_name> and <cluster_domain> with the cluster name and domain you received when you created your Red Hat OpenShift account. Replace <idp_provider_name> with the identity provider name you noted earlier.
Example: https://oauth-openshift.apps.mycluster.mydomain/oauth2callback/myidp
-
In the Duo Admin Panel, scroll down to the bottom of the page and click Save.
Learn more about Red Hat OpenShift SSO at OpenShift Documentation.
Verify SSO
You can log on to Red Hat OpenShift SSO by navigating to your Red Hat OpenShift SSO page e.g., https://console-openshift-console.apps.mycluster.mydomain. Click your identity provider button to be redirected to Duo Single Sign-On to begin authentication.
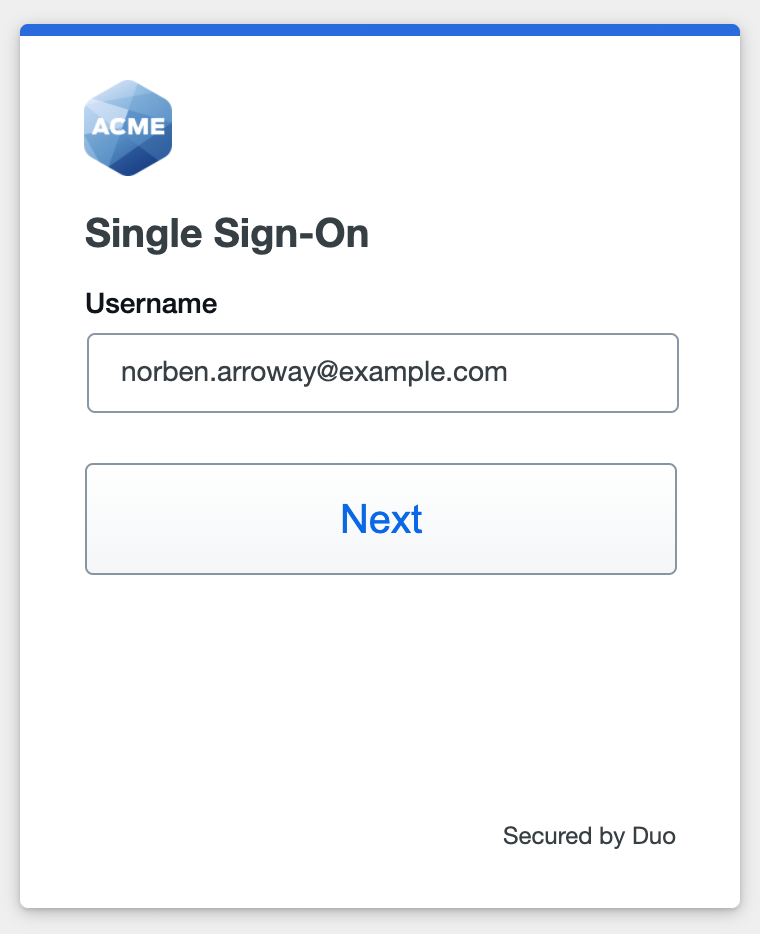
Active Directory Login
With Active Directory as the Duo SSO authentication source, enter the primary username (email address) on the Duo SSO login page and click or tap Next.
Enter the AD primary password and click or tap Log in to continue.
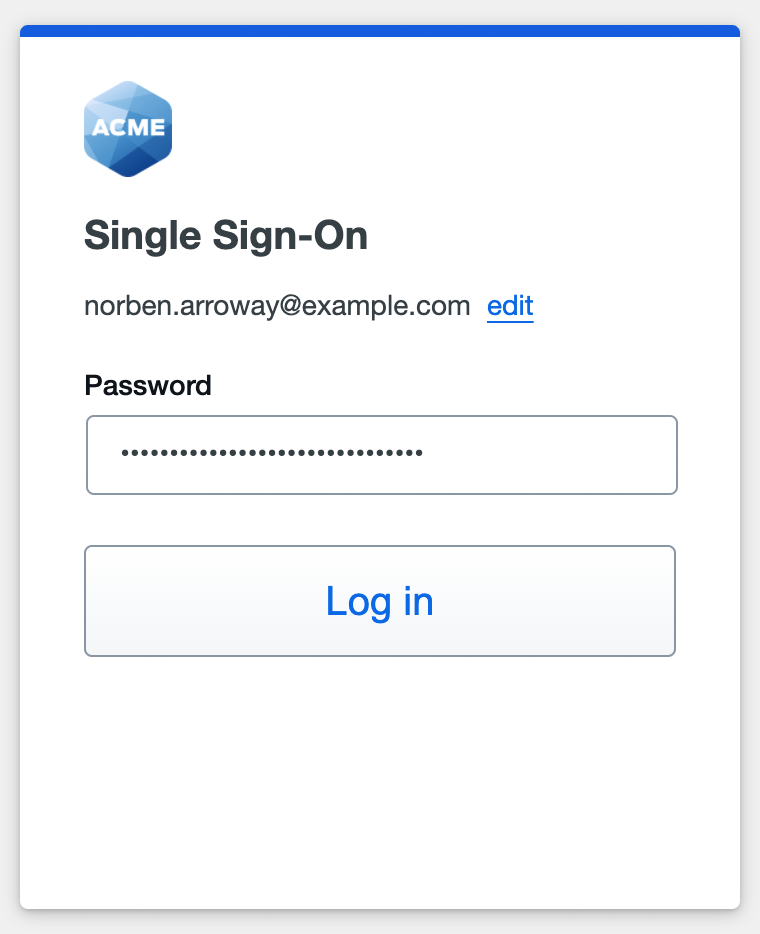
Enable Duo Passwordless to log in to Duo SSO backed by Active Directory authentication without entering a password in the future.
SAML Login
With another SAML identity provider as the Duo SSO authentication source, Duo SSO immediately redirects the login attempt to that SAML IdP for primary authentication. Users do not see the Duo SSO primary login screen.
Duo Authentication
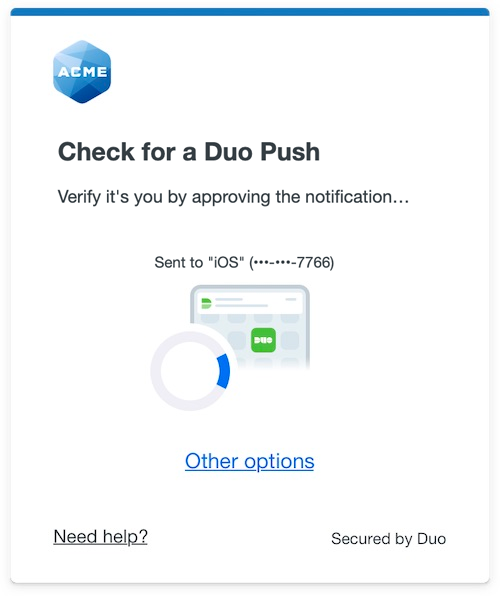
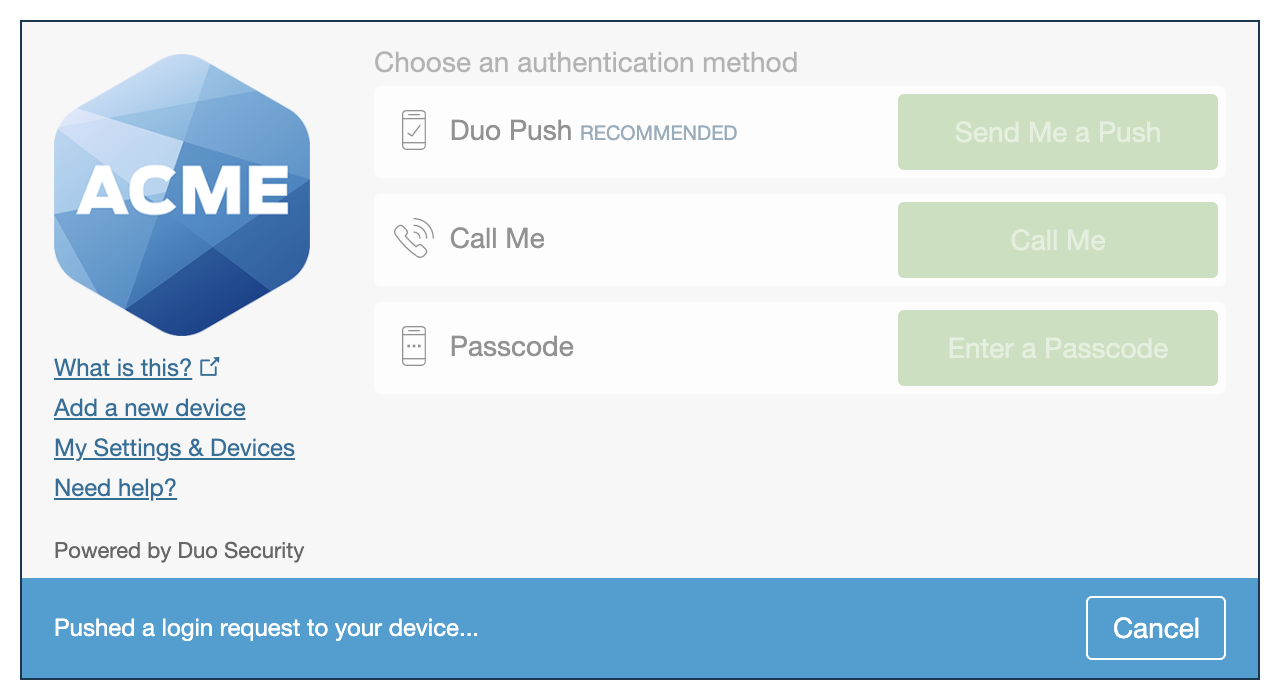
Successful verification of your primary credentials by Active Directory or a SAML IdP redirects back to Duo. Complete Duo two-factor authentication when prompted and then you'll return to Red Hat OpenShift to complete the login process.
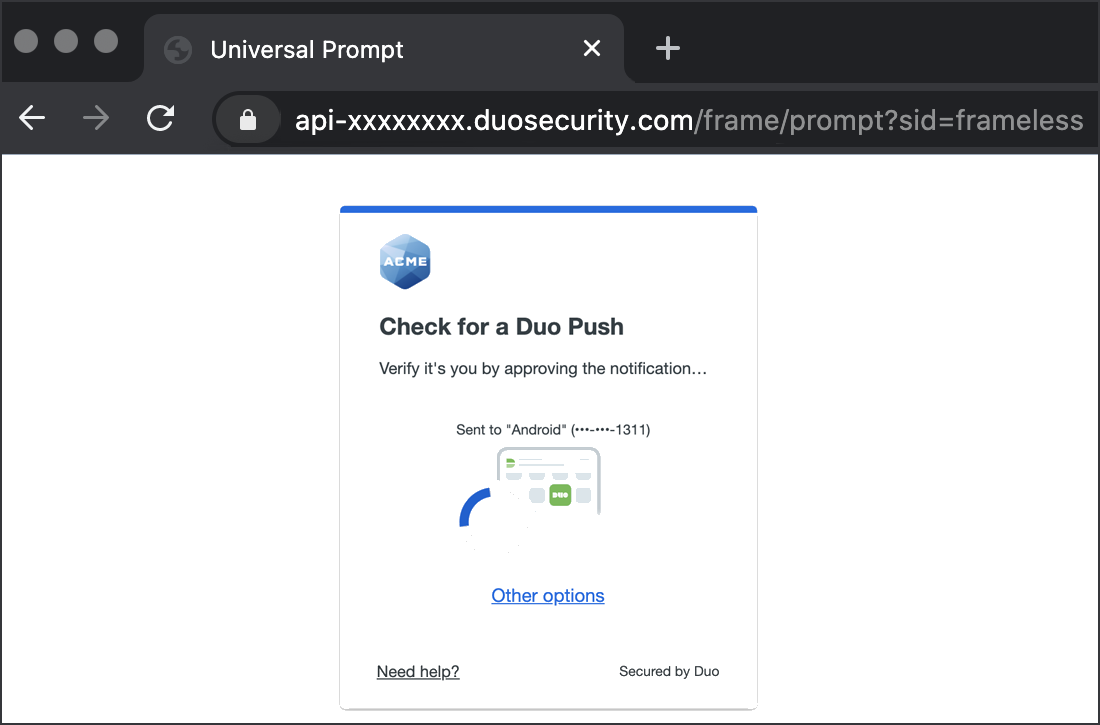
* Universal Prompt experience shown.
Red Hat OpenShift supports SP-initiated authentication only, meaning that you must start your SSO login from that application's sign-in page. You won't be able to add as an application tile in Duo Central for IdP-initiated logins.
Congratulations! Your Red Hat OpenShift users now authenticate using Duo Single Sign-On.
See the full user login experience, including expired password reset (available for Active Directory authentication sources) in the Duo End User Guide for SSO.
Grant Access to Users
If you did not already grant user access to the Duo users you want to use this application be sure to do that before inviting or requiring them to log in with Duo.
Enable Remembered Devices
To minimize additional Duo two-factor prompts when switching between and your other Duo Single Sign-On SAML applications, be sure to apply a shared "Remembered Devices" policy to your SAML applications.
Troubleshooting
Need some help? Try searching our Knowledge Base articles or Community discussions. For further assistance, contact Support.
