Contents
Duo integrates with Atlassian Confluence to add two-factor authentication to your wiki logins, complete with inline self-service enrollment and Duo Prompt. The code is open-source and available on GitHub.
End of Support Information
The last date of support for Duo's two-factor solution for Confluence Server was February 14, 2024. This coincides with Atlassian's end of support for Confluence Server.
Duo will no longer provide updates or fixes for this application, and Duo Support will not provide configuration or troubleshooting assistance.
If you created a Duo Confluence application before February 14, 2024:
- Your existing Duo Confluence installation will continue providing two-factor authentication for user logins past the end of support of the traditional Duo Prompt on March 30, 2024 if you deployed the duo_universal_atlassian plugin.
- If you still use the legacy duo_confluence plugin, it will keep working after March 30, 2024 but will cease working when the future end-of-life date of the traditional Duo Prompt arrives.
- You may view and manage existing Duo Confluence applications in the Duo Admin Panel.
- No new Duo Confluence applications may be created in the Duo Admin Panel.
- Duo no longer provides support or troubleshooting help, except as needed to assist you with migration to Duo Single Sign-On with Atlassian Cloud or Confluence Data Center.
If you did not create a Duo Confluence application before February 14, 2024:
- No new Duo Confluence applications may be created in the Duo Admin Panel.
- Duo no longer provides support or troubleshooting help, except as needed to assist you with migration to Duo Single Sign-On with Atlassian Cloud or Confluence Data Center.
We recommend that you migrate your on-premises Confluence application to Atlassian Cloud and add Duo login protection with Duo Single Sign-On for Atlassian Cloud.
If you opt to deploy Confluence Data Center, you can add Duo login protection with Duo Single Sign-On for Generic SAML Service Providers. The duo_universal_atlassian or duo_confluence MFA plugins are not valid for Confluence Data Center.
Review the Duo End of Sale, Last Date of Support, and End of Life Policy.
Support for the traditional Duo Prompt experience and Duo Prompt delivery via iframe ended on March 30, 2024.
See the update instructions for Confluence to update an existing deployment of the iframe-based Confluence software to the latest release. Authenticating once with the updated Duo software is a required step before you can enable the Duo Universal Prompt for your existing Confluence application.
Please visit the Duo Universal Prompt Update Guide for more information about the traditional Duo Prompt end of support.
This plugin was intended for on-premises installations of Confluence v5 and 6. Check your Confluence version before installing Duo. Also note the location of your Confluence installation directory.
Note that installing Duo may cause issues with application links between Confluence and JIRA. Read this for more information.
First Steps
- Sign up for a Duo account.
- Log in to the Duo Admin Panel and navigate to Applications → Protect an Application.
- Locate the entry for Confluence with a protection type of "2FA" in the applications list. Click Protect to the far-right to configure the application and get your integration key, secret key, and API hostname. You'll need this information to complete your setup. See Protecting Applications for more information about protecting applications with Duo and additional application options.
- Download the latest duo_confluence release package as a zip file from GitHub and uncompress the package on your Confluence server.
The security of your Duo application is tied to the security of your secret key (skey). Secure it as you would any sensitive credential. Don't share it with unauthorized individuals or email it to anyone under any circumstances!
Duo Universal Prompt
The Duo Universal Prompt provides a simplified and accessible Duo login experience for web-based applications, offering a redesigned visual interface with security and usability enhancements.
| Universal Prompt | Traditional Prompt |
 |
 |
Read the Universal Prompt Update Guide for more information about the update process and the new login experience for users.
Migration to Universal Prompt for your Confluence application is a three-step process:
- Install an update for the Confluence application, which implements a redirect to Duo during authentication to support the Universal Prompt.
- Authenticate with Duo 2FA using the updated application so that Duo makes the Universal Prompt activation setting available in the Admin Panel. This first authentication after updating shows the traditional Duo prompt in a redirect instead of an iframe.
- From the Duo Admin Panel, activate the Universal Prompt experience for users of that Duo Confluence application if the traditional prompt is still selected. Once activated, all users of the application see the Duo Universal Prompt in a redirect.
New Confluence Applications
If you're configuring Duo for Confluence for the first time now, we recommend installing the updated Universal Prompt application for Confluence instead of the legacy application described on this page, so your users can experience the Universal Prompt as soon as you finish the Duo configuration steps.
Existing Confluence Applications
Confluence needs a software update installed before you can activate the Universal Prompt experience. The "Universal Prompt" section reflects this status as "Update Required" today.
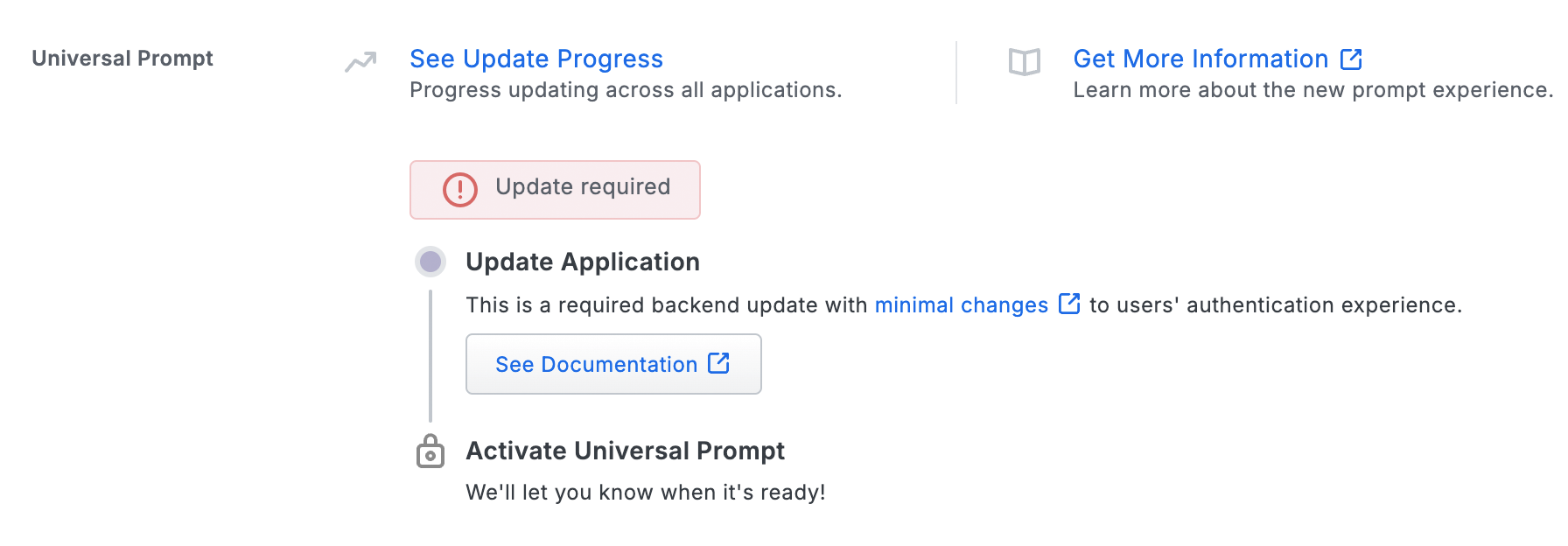
To update your current Confluence Duo application to a newer version so that you can activate the Universal Prompt experience, follow the update directions for the Universal Prompt.
You **must** perform a Duo 2FA authentication after performing the required update. This authentication will not yet show the Universal Prompt, but will update the status of that application in Duo's service to unlock the Universal Prompt activation control so you can then turn it on for the application if the traditional prompt is still selected. Your users continue to see the current Duo prompt experience until you apply the update and authenticate using the updated application, and then activate Universal Prompt for that application.
Universal Update Progress
Click the See Update Progress link to view the Universal Prompt Update Progress report. This report shows the update availability and migration progress for all your Duo applications. You can also activate the new prompt experience for multiple supported applications from the report page instead of visiting the individual details pages for each application.
Install Duo Using a Script
After running the install script you will edit a configuration file, install an add-on with the Confluence UI, and restart Confluence to complete the setup.
From the command line, run the installer from within the duosecurity-duo_confluence directory with the following arguments:
$ ./install.sh -i <your_ikey> -s <your_skey> -h <your_host> -d <confluence_location>
Required Arguments
-i |
Your integration key
(i.e. DIXXXXXXXXXXXXXXXXXX)
|
-s |
Your secret key |
-h |
Your API hostname
(i.e. api-XXXXXXXX.duosecurity.com)
|
Optional Arguments
-d |
The directory where Confluence is installed. Defaults to /opt/atlassian/confluence if not specified. |
The script copies Duo JAR files into your Confluence install directory. If the script is unable to copy the necessary Duo files, try installing Duo manually.
After running the install script, follow the instructions to install the add-on and edit your configuration.
Install Duo Manually
To install the Duo add-on for Confluence manually, first find the top directory of your Confluence installation, called $CONFLUENCE_DIR below. This is usually /opt/atlassian/confluence.
If you've already installed Duo using the install script you don't need to do these manual install steps. Skip to Install the Add-on and Configure Confluence.
-
Copy the prebuilt DuoWeb-1.3.jar from the unzipped etc directory into the Confluence lib directory.
cp etc/DuoWeb-1.3.jar $CONFLUENCE_DIR/confluence/WEB-INF/lib -
Install the duo_client_java JAR
Copy the prebuilt duo-client-0.2.1.jar from the unzipped etc directory into the Confluence lib directory.
cp etc/duo-client-0.2.1.jar $CONFLUENCE_DIR/confluence/WEB-INF/lib -
Copy the prebuilt duo-filter-1.4.3.jar from etc into the Confluence lib directory.
cp etc/duo-filter-1.4.3.jar $CONFLUENCE_DIR/confluence/WEB-INF/lib
After manually copying the JAR files, follow the instructions to install the add-on and edit your configuration.
Install the Add-on and Configure Confluence
-
Install the add-on. The add-on provides the UI to send credentials to Duo and post results back.
From the Confluence administration console, select Add-ons from the left navigation, then Manage add-ons. Click Upload Add-on and browse to the unzipped etc/duo-twofactor-1.4.3.jar file. Click the Upload button.
-
Configure Confluence by editing web.xml, located at $CONFLUENCE_DIR/confluence/WEB-INF/web.xml.
You will add a filter, which can intercept web requests, and a filter mapping, which causes all requests to go through the filter.
The Duo filter must be added immediately after the local authentication filter, which has a filter-name of security, and before any subsequent filters.
Use the appropriate values for
ikey,skey,akey, andhost, as described in Install Duo Using a Script.Your akey is a string that you should generate and keep secret from Duo. It should be at least 40 characters long. You can generate a random string in Python with:
import os, hashlib print hashlib.sha1(os.urandom(32)).hexdigest()Locate the security filter already present in the web.xml file by searching among the
<filter>entries for<filter-name>security</filter-name>. It looks similar to this:<filter> <filter-name>security</filter-name> <filter-class>com.atlassian.confluence.web.filter.ConfluenceSecurityFilter</filter-class> </filter>Paste the below duoauth filter section immediately after the security filter section in web.xml, using your
ikey,skey,akey, andAPI hostvalues:<!-- the duoauth filter and mapping to add, with appropriate param-value entries --> <filter> <filter-name>duoauth</filter-name> <filter-class>com.duosecurity.seraph.filter.DuoAuthFilter</filter-class> <init-param> <param-name>ikey</param-name> <param-value>DXXXXXXXXXXXXXXXXXXX</param-value> </init-param> <init-param> <param-name>skey</param-name> <param-value>abcdefghijklmnopqrstuvwxyx0123456789ABCD</param-value> </init-param> <init-param> <param-name>akey</param-name> <param-value>at_least_40_random_characters_you_make_up</param-value> </init-param> <init-param> <param-name>host</param-name> <param-value>api-XXXXXXXX.duosecurity.com</param-value> </init-param> <!-- set fail.Open to true to fail open or false to fail secure --> <init-param> <param-name>fail.Open</param-name> <param-value>false</param-value> </init-param> </filter>This is the security filter-mapping already present in the web.xml file.
<filter-mapping> <filter-name>security</filter-name> <url-pattern>/*</url-pattern> <dispatcher>REQUEST</dispatcher> <dispatcher>FORWARD</dispatcher> <!-- we want security to be applied after urlrewrites, for example --> </filter-mapping>Paste the below duoauth filter-mapping section immediately after the security filter-mapping section in web.xml.
<filter-mapping> <filter-name>duoauth</filter-name> <url-pattern>/*</url-pattern> <dispatcher>FORWARD</dispatcher> <dispatcher>REQUEST</dispatcher> </filter-mapping> -
Restart Confluence.
- Linux: Run the command
sudo /etc/init.d/confluence stop ; sudo /etc/init.d/confluence start - Windows: Open the "Services" console (services.msc). Locate the Apache Tomcat Confluence service and restart it.
If you haven't configured Confluence to start with a script or service see the Confluence documentation.
- Linux: Run the command
Test your Setup
To test your setup, log into Confluence. Duo's enrollment or login prompt should appear after you enter your username and password.
If you plan to permit use of WebAuthn authentication methods (security keys, U2F tokens, or Touch ID) in the traditional Duo Prompt, Duo recommends configuring allowed hostnames for this application and any others that show the inline Duo Prompt before onboarding your end-users.
The Duo Universal Prompt has built-in protection from unauthorized domains so this setting does not apply.
Updating the Duo Plugin
Please see the instructions for updating the v1.x Confluence plugin to the Duo Atlassian 2.x plugin, featuring support for the Duo Universal Prompt.
Notes
To deactivate the filter, remove or comment out the filter mapping from web.xml and restart Confluence. Duo authentication is no longer required.
XML-RPC and SOAP are not authenticated with Seraph unless an empty authentication token is used. For more information, see Managing Confluence Users - Authentication
Troubleshooting
Need some help? Take a look at our Confluence Knowledge Base articles or Community discussions. For further assistance, contact Support.
Network Diagram
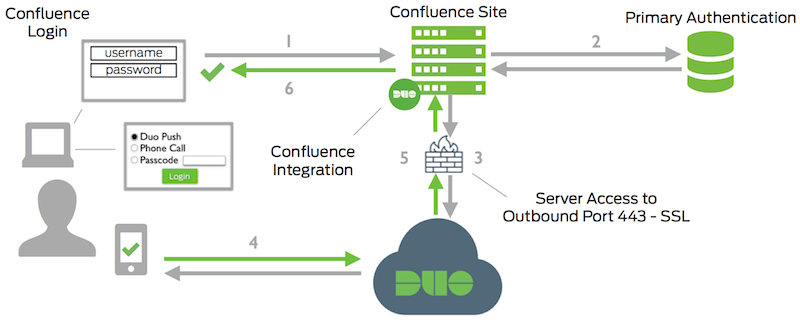
- Confluence connection initiated
- Primary authentication
- Confluence connection established to Duo Security over TCP port 443
- Secondary authentication via Duo Security’s service
- Confluence receives authentication response
- Confluence session logged in
Appendix: Building Manually
JARs and templates are located in the etc directory. If you'd prefer to build your own JARs, here is how to do it. The add-on JAR must be rebuilt if you want to customize the Duo authentication page.
-
Build the duo web JAR
If you'd prefer to build your own DuoWeb-1.3.jar, the latest duo_java release source is available from Github. It can be built with the Atlassian plugin SDK. In a temporary directory:
git clone git://github.com/duosecurity/duo_java.git cd duo_java/DuoWeb atlas-mvn installAfter this step, the built JAR can be copied to the Confluence lib directory as described in Install the duo web JAR.
-
Build the duo client JAR If you'd prefer to build your own duo-client-0.2.1.jar, the duo_client_java source is available from Github. It can be build with the Atlassian plugin SDK. In a temporary directory:
git clone git://github.com/duosecurity/duo_client_java cd duo_client atlas-mvn installAfter this step, the built JAR can be copied to the Confluence lib directory as described in Install the duo_client_java JAR
-
Build the Add-on JAR
Optionally Customize the Duo Authentication Page
The authentication page template is duo_twofactor/src/main/resources/duologin.vm. It can be used as-is, or styled to match your organization.
If you want the Duo authentication page to include other resources, such as scripts or images, put them in the resources directory as well, and edit atlassian-plugin.xml to add them to the served resources. After customizing, rebuild and install the JAR.
Build the JAR
If you'd prefer to build your own duo-twofactor-1.4.3.jar, it can be built with the Atlassian plugin SDK from the latest duo_confluence release source from GitHub:
cd duo_twofactor atlas-mvn packageAfter this step, the built JAR can be installed as described in Install the add-on.
-
Build the Seraph Filter JAR
If you'd prefer to build your own duo-filter-1.4.3.jar, i it can be built with the Atlassian plugin SDK from the latest duo_confluence release source from GitHub.
The seraph filter has duo_java and duo_client_java as build dependencies. Please follow the instructions for manually building duo_java and duo_client_java before attempting a manual build of the seraph filter.
cd duo_seraph_filter atlas-mvn packageAfter this step, the built JAR can be installed as described in Install the Seraph filter.
