Documentation
Duo Trusted Endpoints - Sophos Mobile Managed Device Deployment
Last Updated: October 31st, 2024Contents
Certificate-based Trusted Endpoint verification for Sophos Mobile reached end-of-life on October 7, 2024. Duo device certificates will no longer renew after October 2024. Migrate existing iOS Certificate Configuration management integrations to iOS Configuration. Learn more about the end-of-life timeline and migration options in the Duo Trusted Endpoints Certificate Migration Guide.
Duo's Trusted Endpoints feature secures your sensitive applications by ensuring that only known devices can access Duo protected services. When a user authenticates via the Duo Prompt, we'll check for the access device's management status. You can monitor access to your applications from trusted and untrusted devices, and optionally block access from devices not trusted by your organization.
Trusted Endpoints is part of the Duo Essentials, Duo Advantage, and Duo Premier plans.
Before enabling the Trusted Endpoints policy on your applications, you'll need to configure REST API access for Duo to your managed mobile devices or apply a compliance policy which includes Duo Mobile. This guide walks you through Sophos Mobile configuration for Android and iOS mobile devices.
Mobile Trusted Endpoints and Verified Duo Push: Trusted endpoint verification of iOS and Android devices with Duo Mobile uses the standard Duo Push approval process and will not prompt for a Duo Push verification code, even if the effective authentication methods policy for the user and application has "Verified Duo Push" enabled.
Compatibility
This trusted endpoints integration supports Sophos Mobile version 8.0 and later when managed by Sophos Mobile Admin. It is not compatible with Sophos Central solutions.
Prerequisites
-
Access to the Duo Admin Panel as an administrator with the Owner, Administrator, or Application Manager administrative roles.
-
Access to Sophos Mobile Admin as an administrator with the rights to create administrators, modify system setup settings, create and apply profiles and policies, and enroll devices.
-
If you plan to trust Android devices, you should have already configured Android Enterprise in Sophos Mobile and Android enterprise device enrollment.
-
If you plan to trust iOS devices, you should have already configured Apple Push Notification service certificates.
Android Configuration
Duo determines trusted device status on Android devices with Duo Mobile installed and activated for Duo Push using the Sophos Mobile API to verify device information. To enable this verification you'll need to grant Duo's service API access in Sophos Mobile.
Create the Sophos Mobile Integration
- Log in to the Duo Admin Panel and navigate to Devices → Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Management Tools Integration" page, locate Sophos Mobile in the list of "Device Management Tools" and click the Add this integration selector.
- Choose Android from the "Recommended" options, and then click the Add button.
The new Sophos Mobile integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
Please note that this integration takes advantage of managed app configuration and therefore Duo Mobile must be installed by your MDM for the device to be considered trusted.
Keep the Duo Admin Panel open in your browser. You'll need to refer back to the Sophos Mobile management integration page to complete the Android configuration steps.
Configure Duo Mobile Distribution
-
If you did not previously set up Android Enterprise you must complete it now to continue.
-
Log on to Sophos Mobile Admin and navigate to Configure → Apps → Android.
-
Click Open managed Google Play, search for Duo Mobile, click Select next to Duo Mobile, and then approve the app.
-
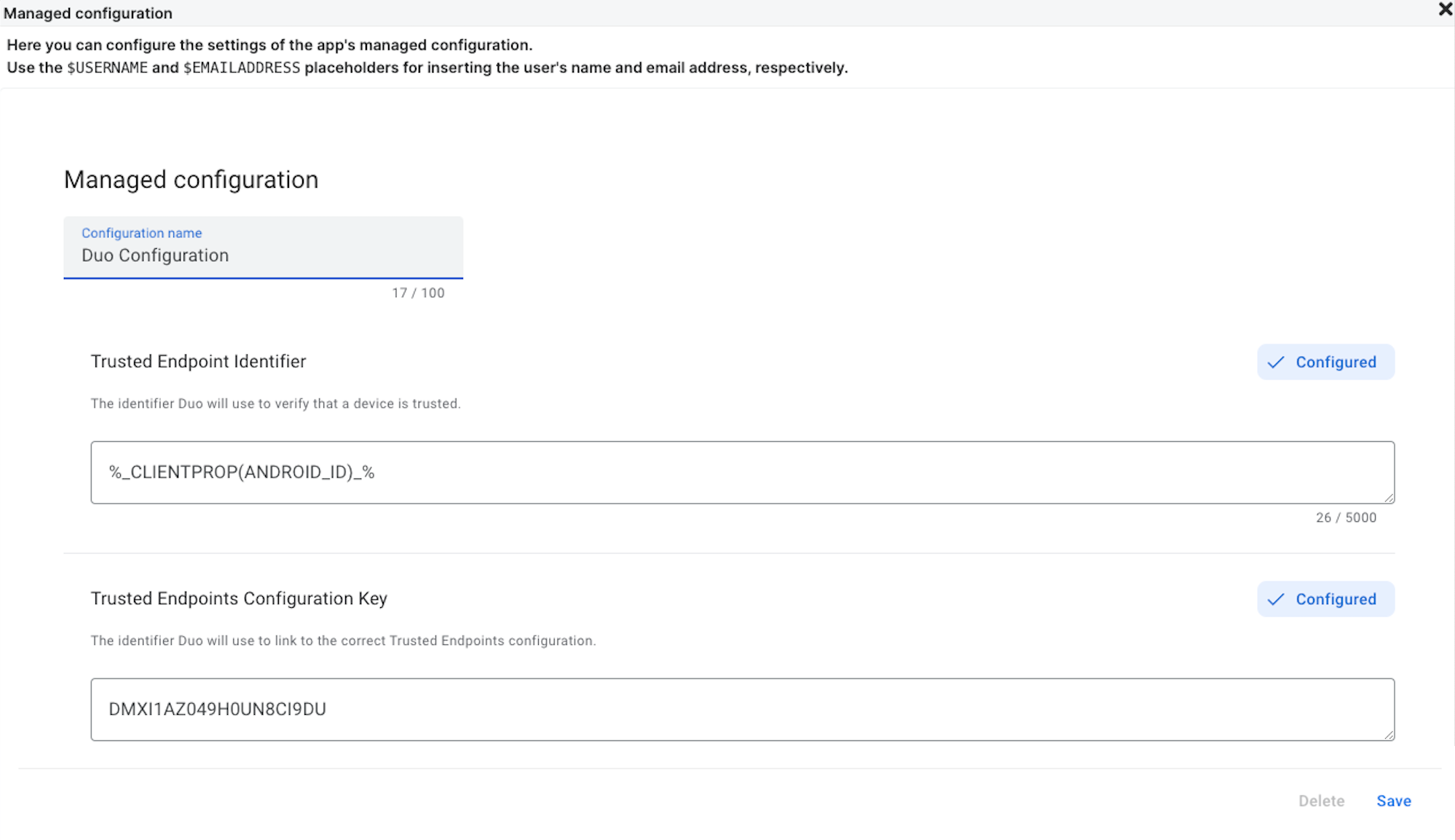
Click on Duo Mobile in the approved apps list and select Edit Managed Configuration to edit the app's properties.
-
Locate the "Trusted Endpoint Identifier" managed configuration field and enter %CLIENTPROP(ANDROID_ID)% as the value.
-
Return to the Duo Admin Panel. Copy the Trusted Endpoints configuration key value (it will look similar to DJPO0S0HLJD0ASDHTDD) and paste it into the Sophos Mobile Admin Trusted Endpoints Configuration Key field.
-
Click Save to return to the "Approved apps" page.
Modify Firewall Rules for Duo
If using an on-premises installation of Sophos Mobile you may need to modify your firewall rules so that Sophos Mobile can communicate with Duo's service.
Use the IP ranges shown under the "Add a Firewall Rule" section on the Sophos Mobile management integration page in the Duo Admin Panel when updating your firewall rules and verifying connectivity.
Create an Administrator for Duo
-
While still logged into Sophos Mobile Admin, go to Settings Setup → Administrators.
-
Click on Create administrator.
-
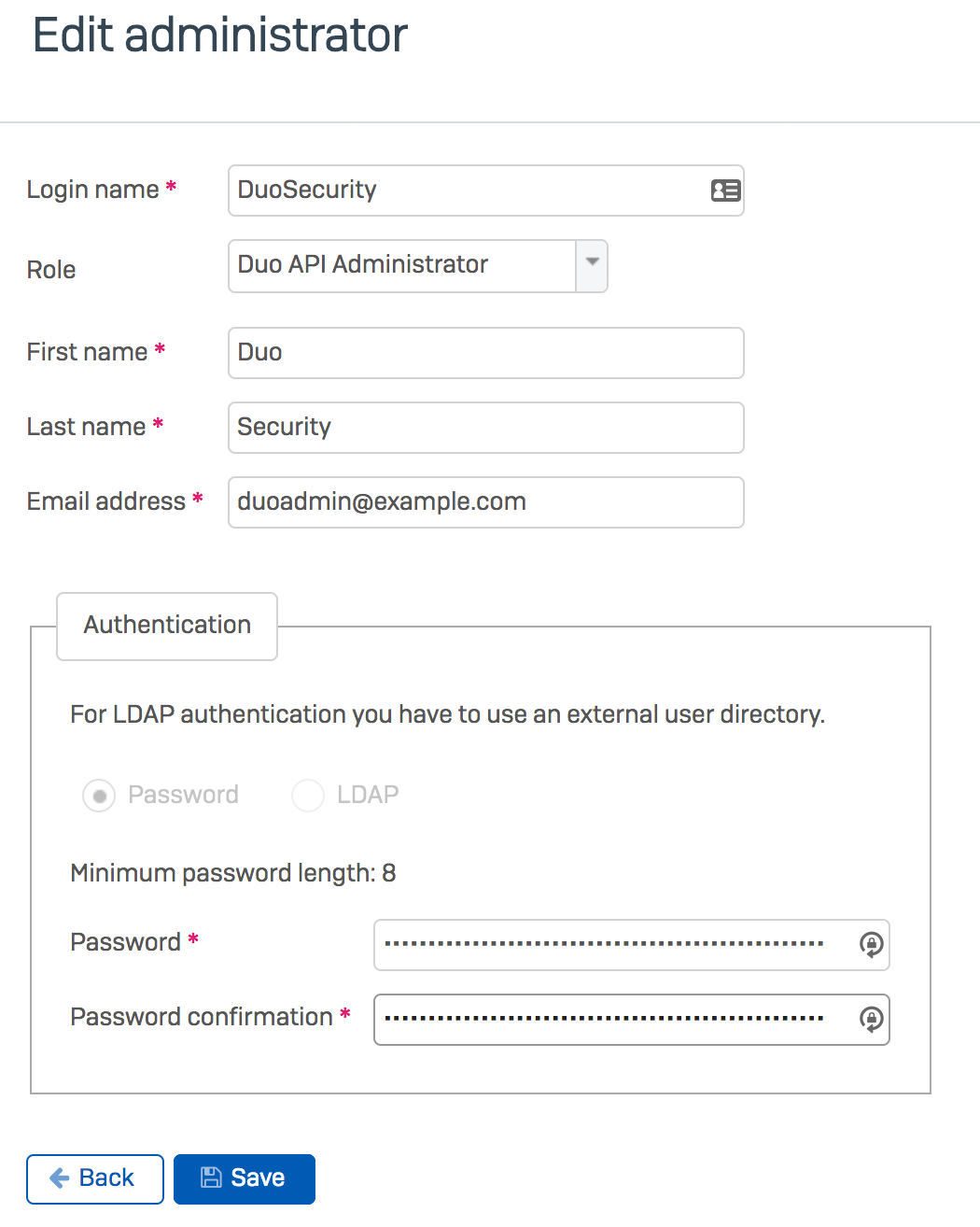
Enter the following information:
Username Enter the desired Duo account username. Role Set to Duo API Administrator First Name and Last Name Enter a first and last name for the Duo admin user (e.g. "Duo" "Admin"). Email Address Enter an email address for your Duo admin user. Password and Confirm Password Enter and confirm a strong password for the Duo admin user. You will enter this password in the Duo Admin Panel in the next steps. -
Click Save.
Enter Sophos Mobile Info in Duo
-
Return to the Duo Admin Panel. Enter the following information into the blank fields under the "Enter Administrator's Credentials" section:
Login Name Enter the Duo API Administrator username you created in Sophos Mobile. Password Enter the password for the Duo API Administrator you created in Sophos Mobile. Customer Enter your organization's Sophos Mobile customer name, used when logging into Sophos Mobile Admin. Domain of Sophos Mobile Instance Enter your organization's Sophos Mobile domain. For example, if you access the Sophos Mobile console at https://abc123.sophosmc.comthen you'd enterabc123.sophosmc.comas the domain name. -
Click the Test Configuration button to verify Duo's API access to your Sophos Mobile instance. You'll receive a "Configuration Successful!" message if everything's correct. If the test fails, verify that you completed the Sophos Mobile configuration steps and entered the right information in the Duo Admin Panel.
-
After you successfully test your configuration, click the Save & Configure button.
At this point the configured integration is disabled and applies to no users until you finish your deployment.
iOS Configuration
Duo determines trusted device status on iOS devices with Duo Mobile installed and activated for Duo Push using Sophos Mobile to push information to mobile devices, which Duo collects at time of authentication.
Create the Sophos Mobile with App Config Integration
- Log in to the Duo Admin Panel and navigate to Devices → Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Management Tools Integration" page, locate Sophos Mobile in the list of "Device Management Tools" and click the Add this integration selector.
- Choose iOS from the "Recommended" options, and then click the Add button.
The new Sophos Mobile with App Config integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
Please note that this integration takes advantage of managed app configuration and therefore Duo Mobile must be installed by your MDM for the device to be considered trusted.
Keep the Duo Admin Panel open in your browser. You'll need to refer back to the Sophos Mobile with App Config management integration page to complete the configuration steps.
Configure Duo Mobile Distribution
-
If you did not previously set up Apple Push Notification service certificates in Sophos Mobile you must complete it now to continue.
-
Log on to Sophos Mobile Admin and navigate to Configure → Apps → iOS & iPadOS.
-
Click Add App and choose iOS link.
-
On the "Edit iOS app" page, click the Search in App Store button. Search for and select Duo Mobile. Ensure that the Sophos Mobile managed installation option is enabled (checked).
-
Locate the "Settings and VPN" item and click the Show button to the right.
-
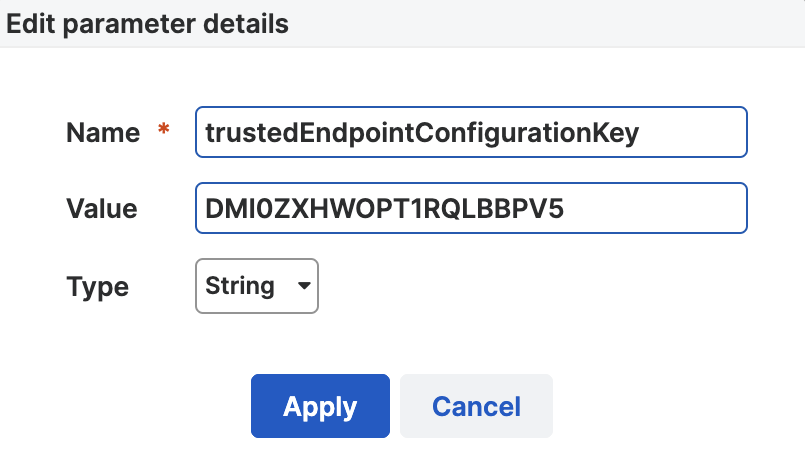
In the "Managed configuration" section of the "Edit settings and VPN" page, click the Add parameter button. Return to the Duo Admin panel and use the information there to add a new key parameter in Sophos Mobile:
Name Copy the Key from the "Trusted Endpoints configuration key" section in the Duo Admin Panel. Value Copy the Value from the "Trusted Endpoints configuration key" section in the Duo Admin Panel. Type Select String. -
Click Apply.
-
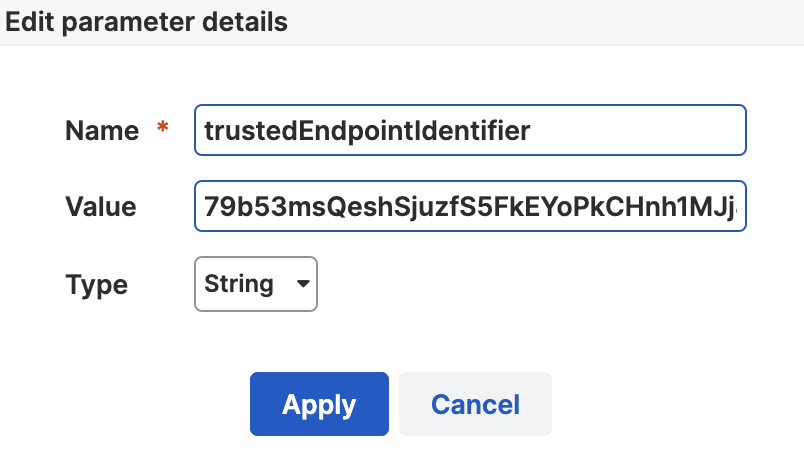
Click the Add parameter button again to add a second parameter. Return to the Duo Admin panel and use the information there to add a new parameter in Sophos Mobile:
Name Copy the Key from the "Trusted Endpoints identifier" section in the Duo Admin Panel. Value Copy the Value from the "Trusted Endpoints identifier" section in the Duo Admin Panel. Protect the Duo Trusted Endpoint Identifier value as a secret and do not share it with anyone. Type Select String. -
Click Apply.
-
Click Apply on the "Edit settings and VPN page and then click Save.
Automate Duo Mobile Installation
To auto-deploy the Duo Application to Sophos managed devices, create and apply a Sophos compliance policy to a device group. Before you can do this, you'll need to first create an App Group and Task Bundle.
Configure Sophos App Group
For more information about Sophos App Groups, please refer to the Sophos Mobile on Premise documentation or the Sophos Mobile documentation.
-
In the Sophos Mobile Admin dashboard, navigate to Settings → App Groups → iOS & iPadOS.
-
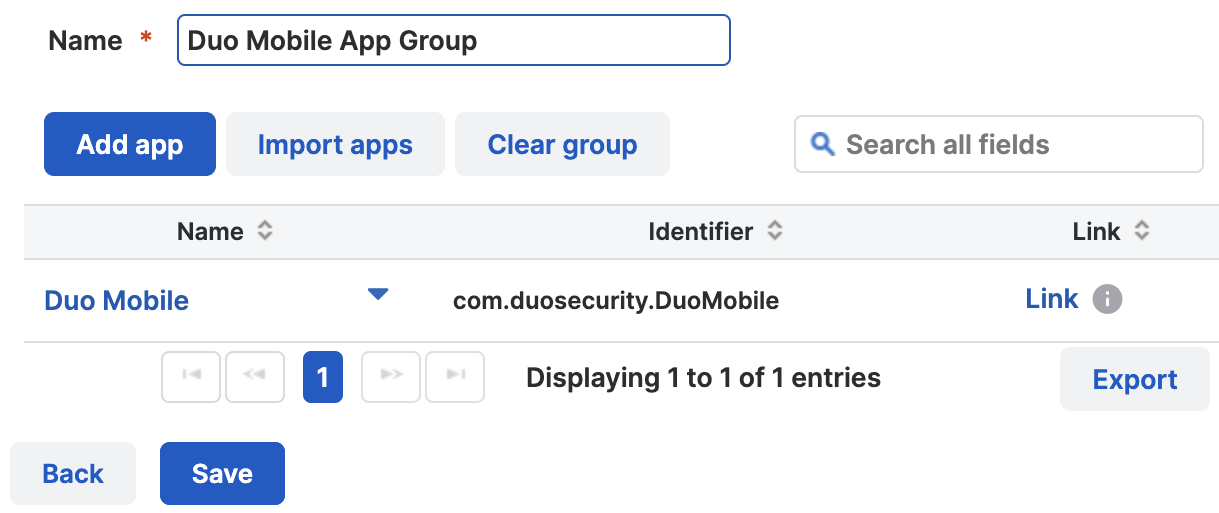
Click Create to create a new app group, or select an existing app group. If you're creating a new app group, give it a descriptive name, like "Duo Mobile App Group".
-
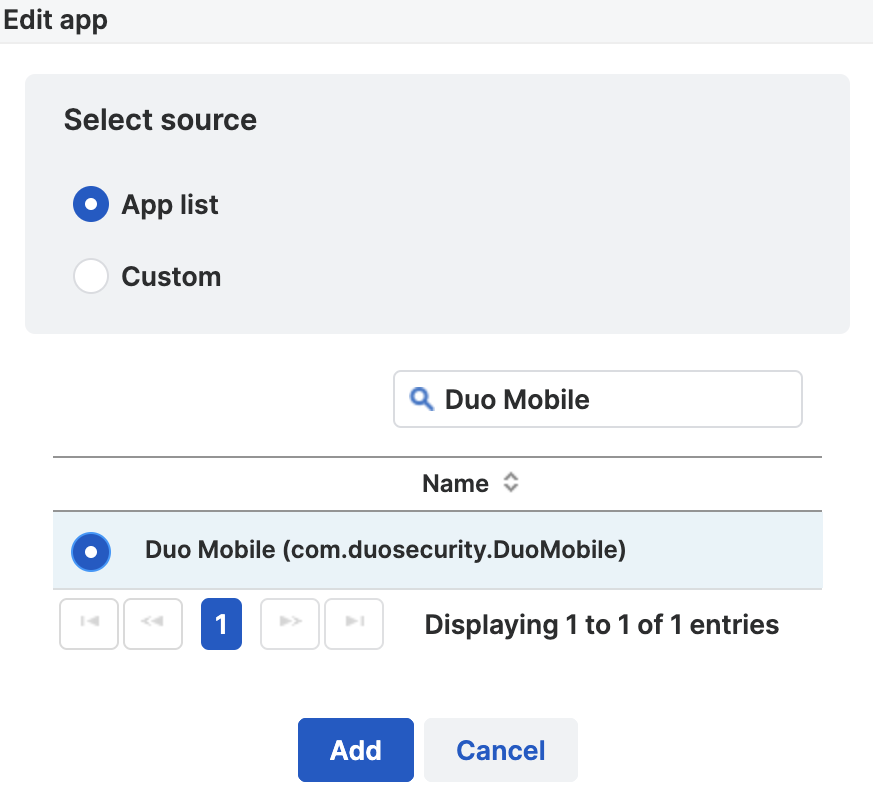
Click Add App, and then search for and select Duo Mobile. Click Add.
-
Review the "Edit app group" page to verify the app information, and then click Save.
Configure Sophos Task Bundle
For more information about Sophos Task Bundles please visit the Sophos Mobile on Premise documentation or the Sophos Mobile documentation.
-
In the Sophos Mobile Admin dashboard, navigate to Configure → Task Bundles → iOS & iPadOS.
-
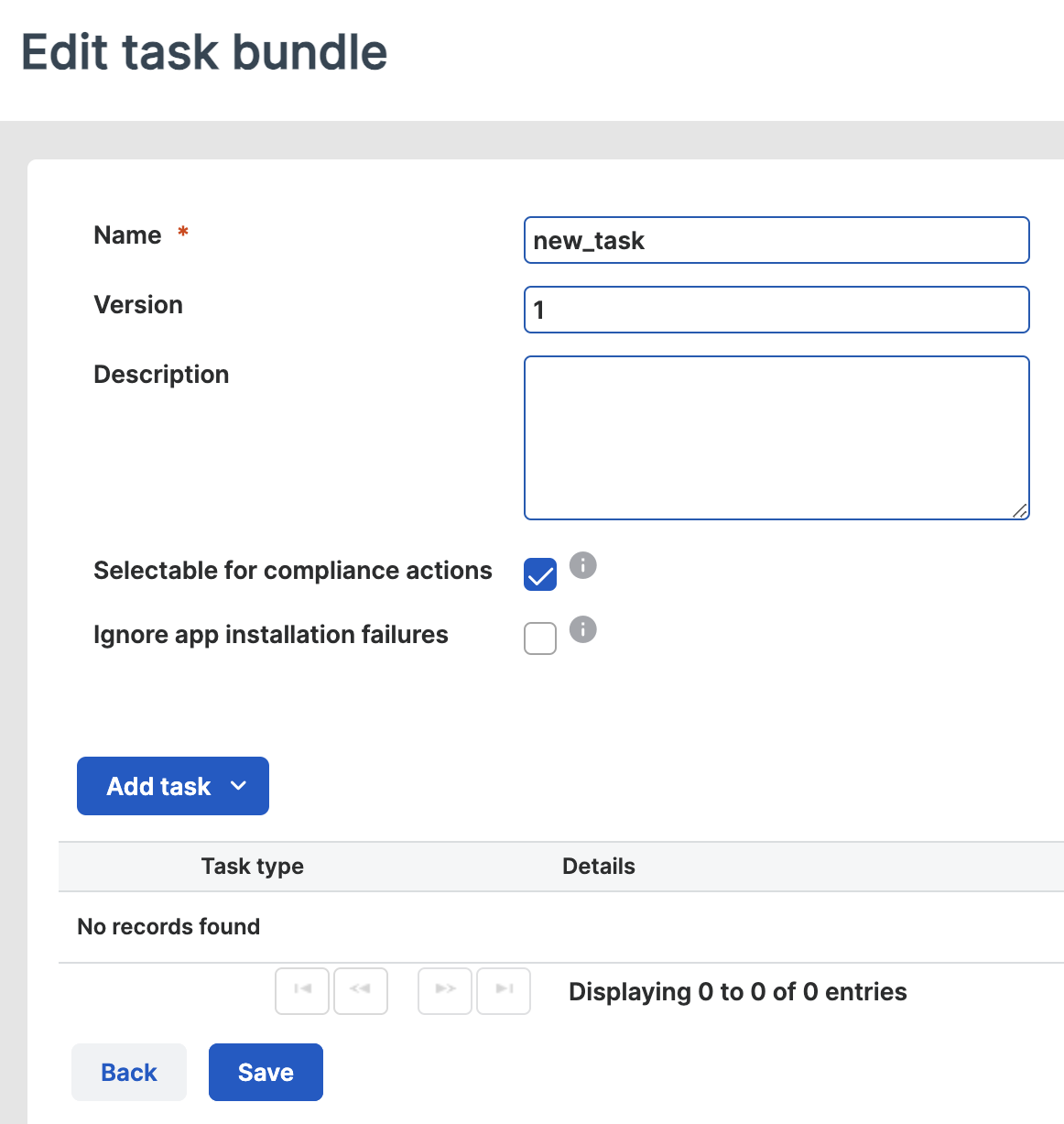
Click Create to create a new task bundle, or select an existing bundle to which you'll add the Duo task.
-
On the "Edit task bundle" page, give the new task bundle a name and enable the Selectable for compliance actions option by checking the box.
-
Click Add task and select Install app from the options.
-
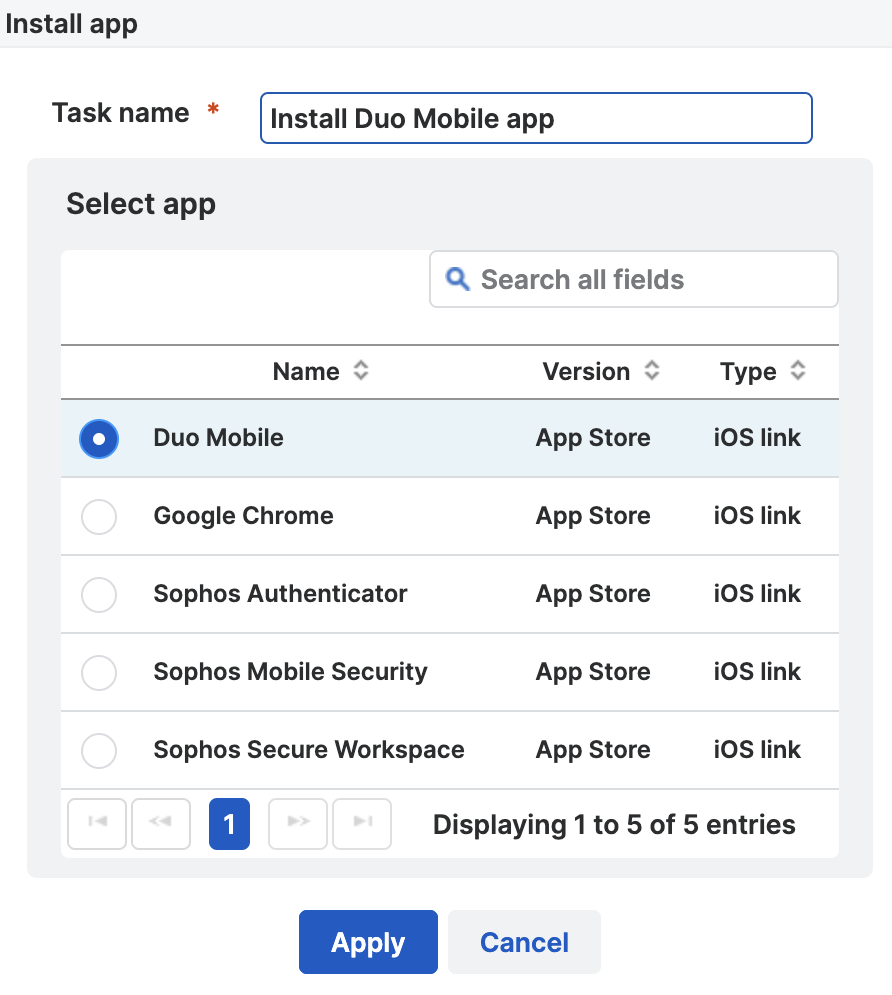
Give the new task a descriptive name, like "Install Duo Mobile app", and then search for and select Duo Mobile.
-
Click Apply to add the new task to the bundle, and then click Save to save the change to the task bundle.
Configure Sophos Compliance Policy
For more information about the Sophos Compliance Policies please visit the Sophos Mobile on Premise documentation or the Sophos Mobile documentation.
-
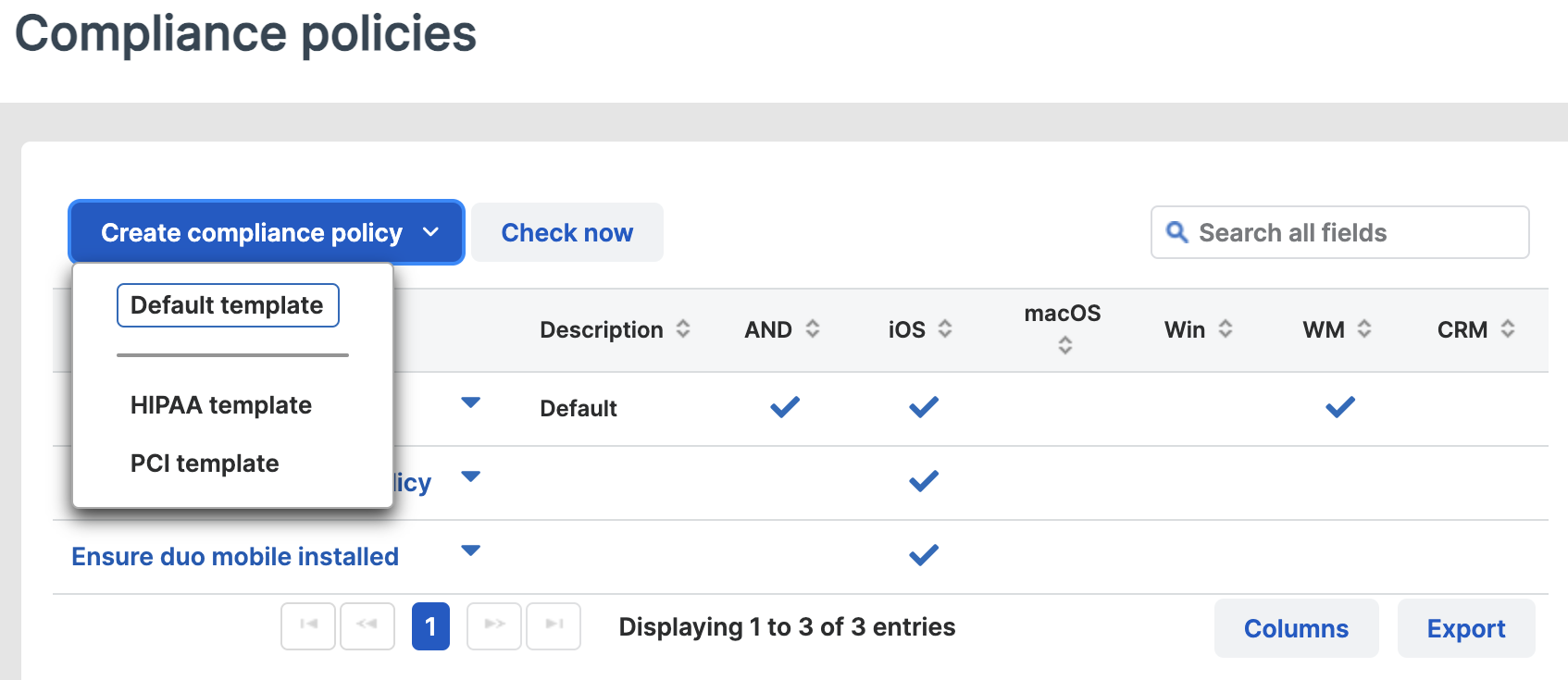
In the Sophos Mobile Admin dashboard, navigate to Configure → Compliance policies.
-
Click Create compliance policy to create a new compliance policy, or select an existing policy to edit for Duo. If you're creating a new policy, select Default Template from the drop-down options.
-
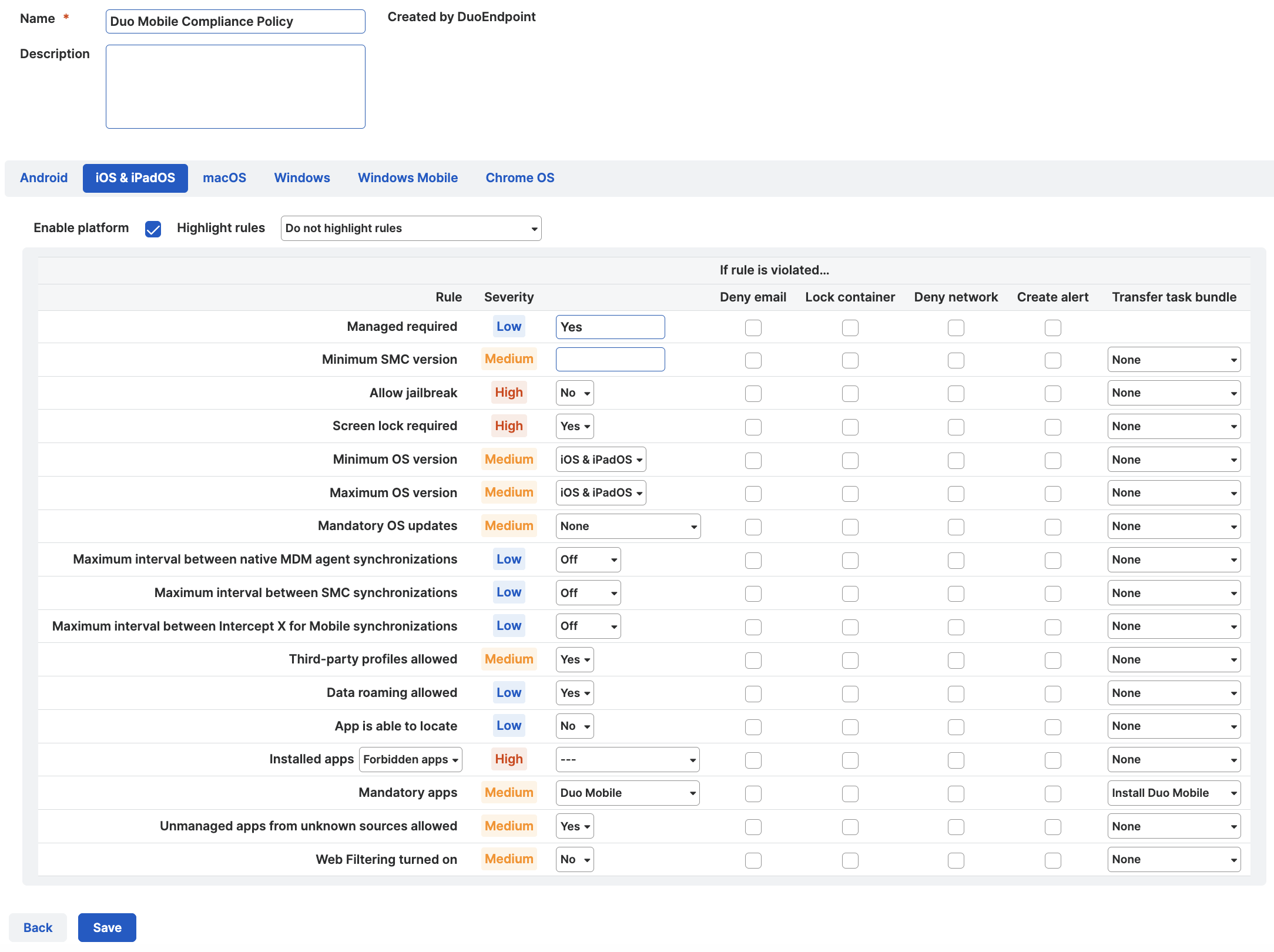
Give the new policy a name, and click the iOS & iPadOS tab.
-
Locate the Mandatory apps rule in the list, and use the drop-down to select the app group you created or updated to add Duo Mobile.
-
Set the Transfer task bundle in the "Mandatory apps" row to the task bundle you configured to install Duo Mobile.
-
If you created a new policy, disable the Enable platform option on each of the operating system tabs other than the "iOS & iPadOS" tab. Click Save.
Apply Sophos Compliance Policy to Device Groups
For more information about applying Sophos compliance policies to device groups please visit the Sophos Mobile on Premise documentation or the Sophos Mobile documentation.
-
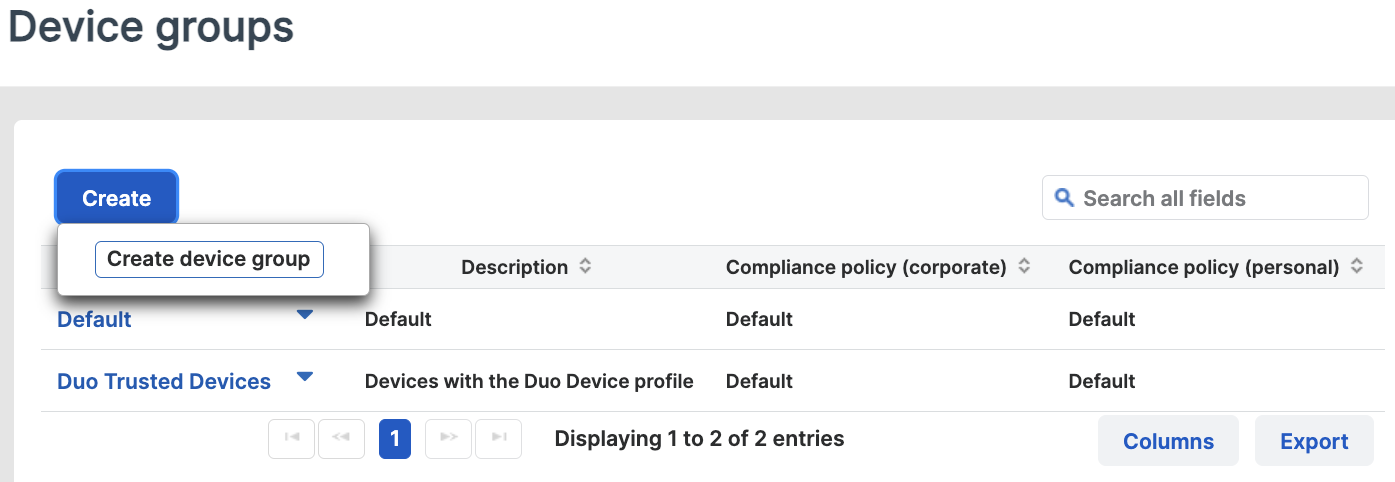
In the Sophos Mobile Management dashboard, navigate to Manage → Device Groups.
-
Click Create to create a new device group, or select an existing group to which you'll apply the Duo compliance policy.
-
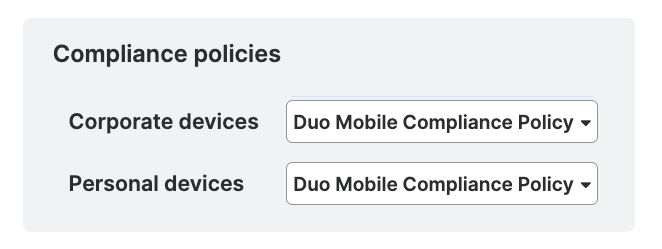
Select the compliance policy you created or modified earlier for Duo Mobile from the drop-down for both Corporate devices and Personal devices.
-
Click Save.
iOS Certificate Configuration
End of Life Information
New Sophos certificate deployment management integrations may no longer be created as of October 2021, and reached end of life on October 7. 2024. Duo device certificates will no longer renew after October 2024. You must migrate your certificate-based iOS Sophos integration to Sophos Mobile with App Config. See the Duo Knowledge Base article Guide to updating Trusted Endpoints iOS integrations from certificates to AppConfig for more information about migrating your iOS certificate-based management integrations to App Config.
Use of the Duo Desktop for trust attestation provides several advantages over the use of device certificates:
- It provides a more accurate assessment of your managed devices, and removes concerns about long-lived certificates present on devices no longer managed by your organization.
- It extends support to Firefox users. Trusted Endpoint certificate detection only works with Chrome, Edge, Safari, and Internet Explorer (depending on the management system).
- Improves trust detection for web browsers and thick client applications.
See the Duo Trusted Endpoints Certificate Migration Guide for more information.
Finish Trusted Endpoints Deployment
Once your Sophos Mobile managed devices receive the Duo config you can set the Trusted Endpoints policy to start checking for managed device status as users authenticate to Duo-protected services and applications.
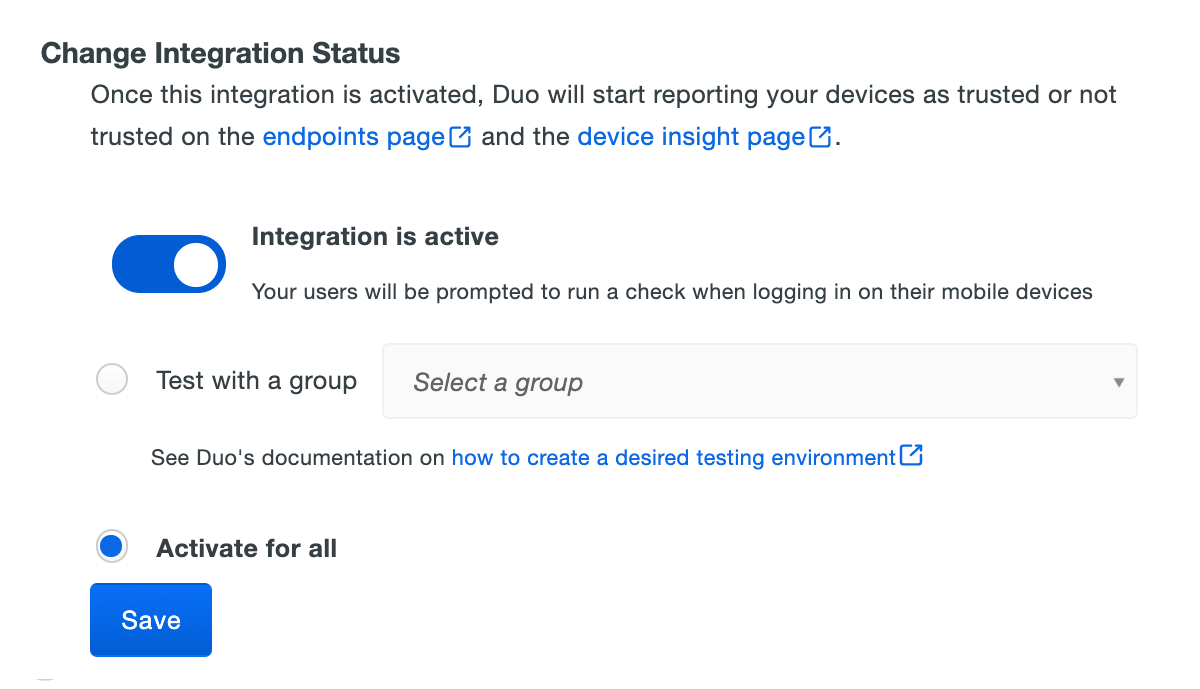
When your trusted endpoints policy is applied to your Duo applications, return to the Sophos Mobile trusted endpoint management integration in the Admin Panel. The "Change Integration Status" section of the page shows the current integration status (disabled by default after creation). You can choose to either activate this management integration only for members of a specified test group, or activate for all users. If you created more than one Sophos Mobile integration, you must activate each one individually.
Duo Premier and Duo Advantage plans: The Device Insight and Endpoints pages in the Duo Admin Panel show which access devices are trusted/managed.
Verify Your Setup
Users with Duo Mobile installed and activated for Duo Push on Android and iOS devices see a device trust dialog when authenticating to a protected resource via the Duo Prompt.
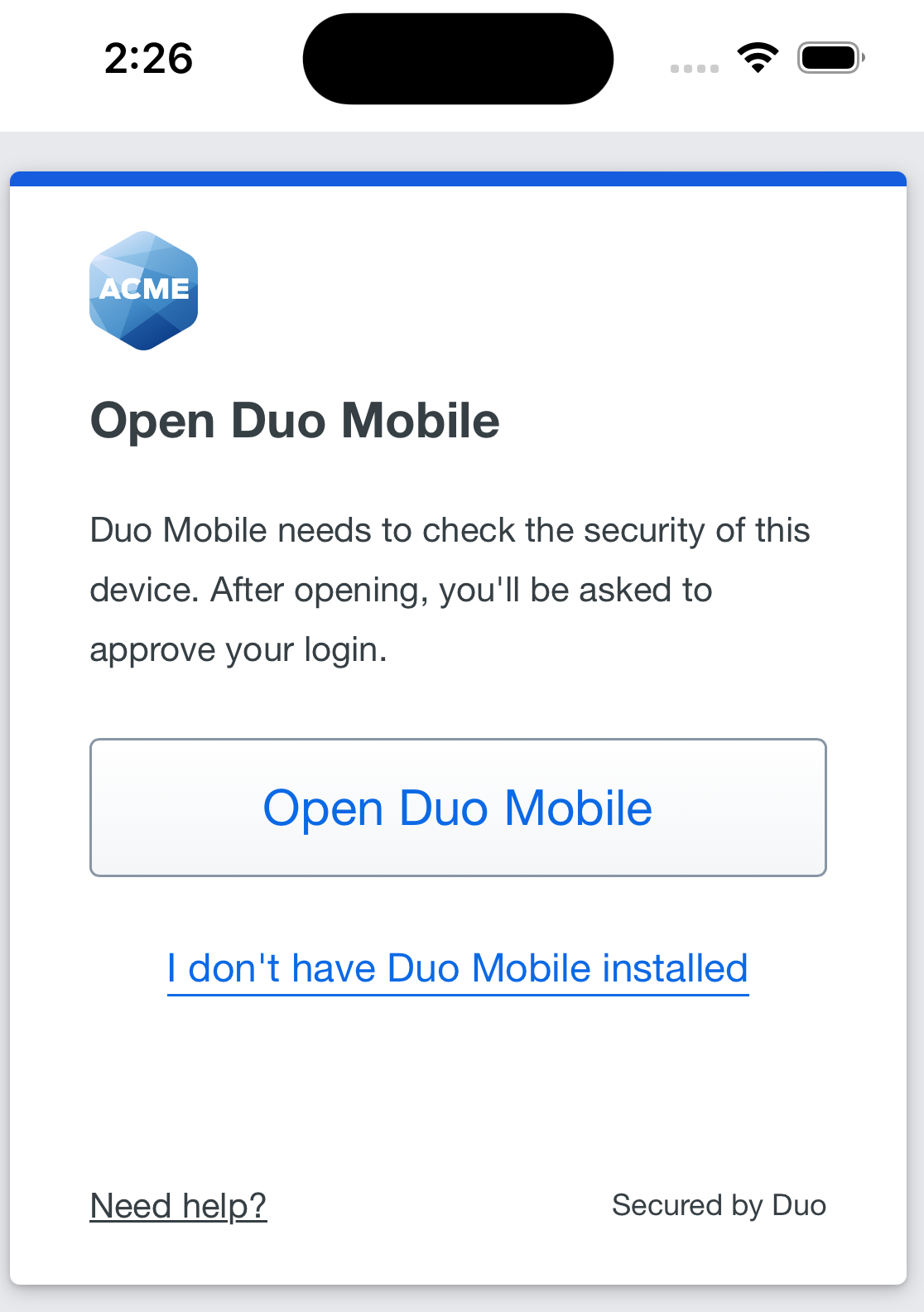
Duo uses the API access you granted in Sophos or the app policy configuration to perform a permissions check to verify device information.
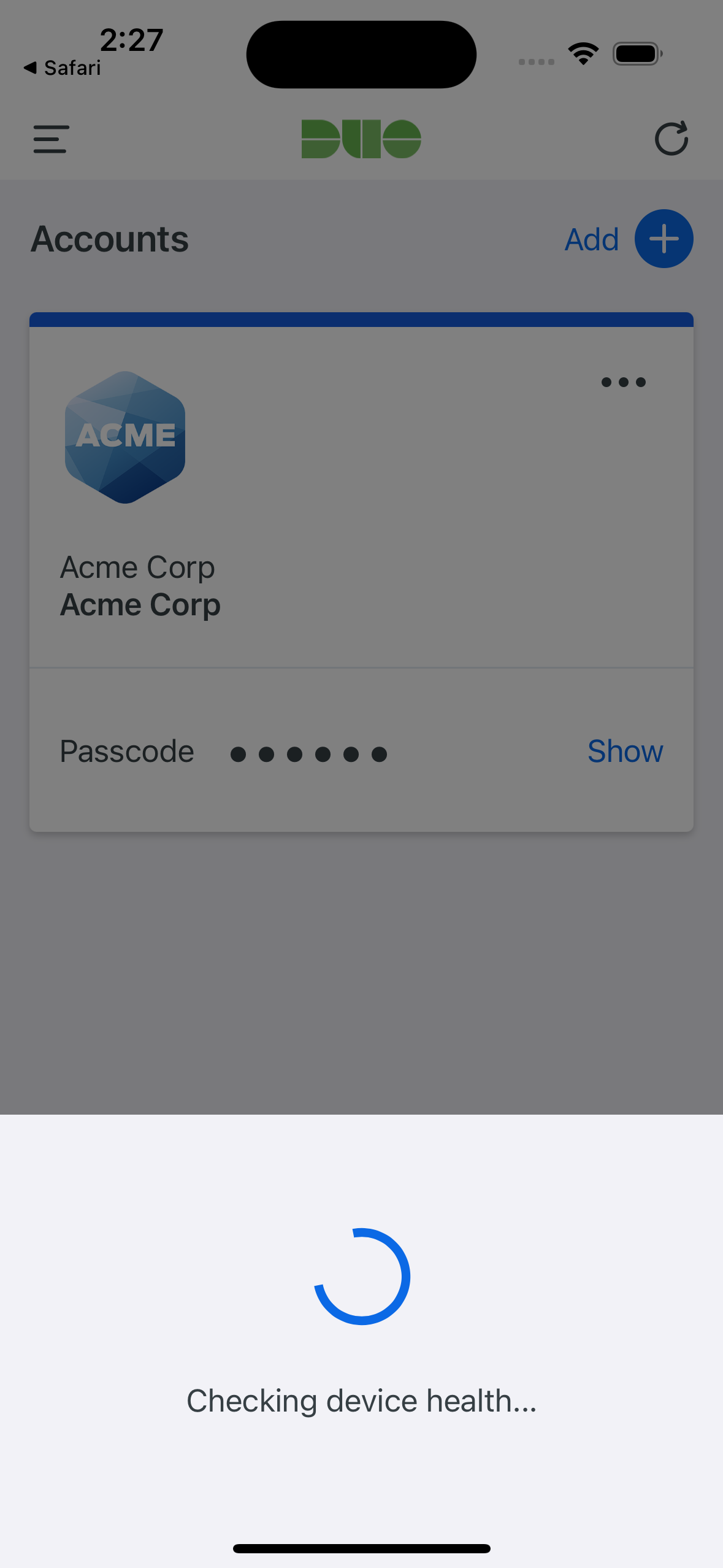
If Duo successfully verifies the device information, then the user receives a login request on their phone. Approving the request grants access to the protected application. The "Second Factor" logged for these approvals is shown as "Duo Mobile Inline Auth" in the Duo authentication log.
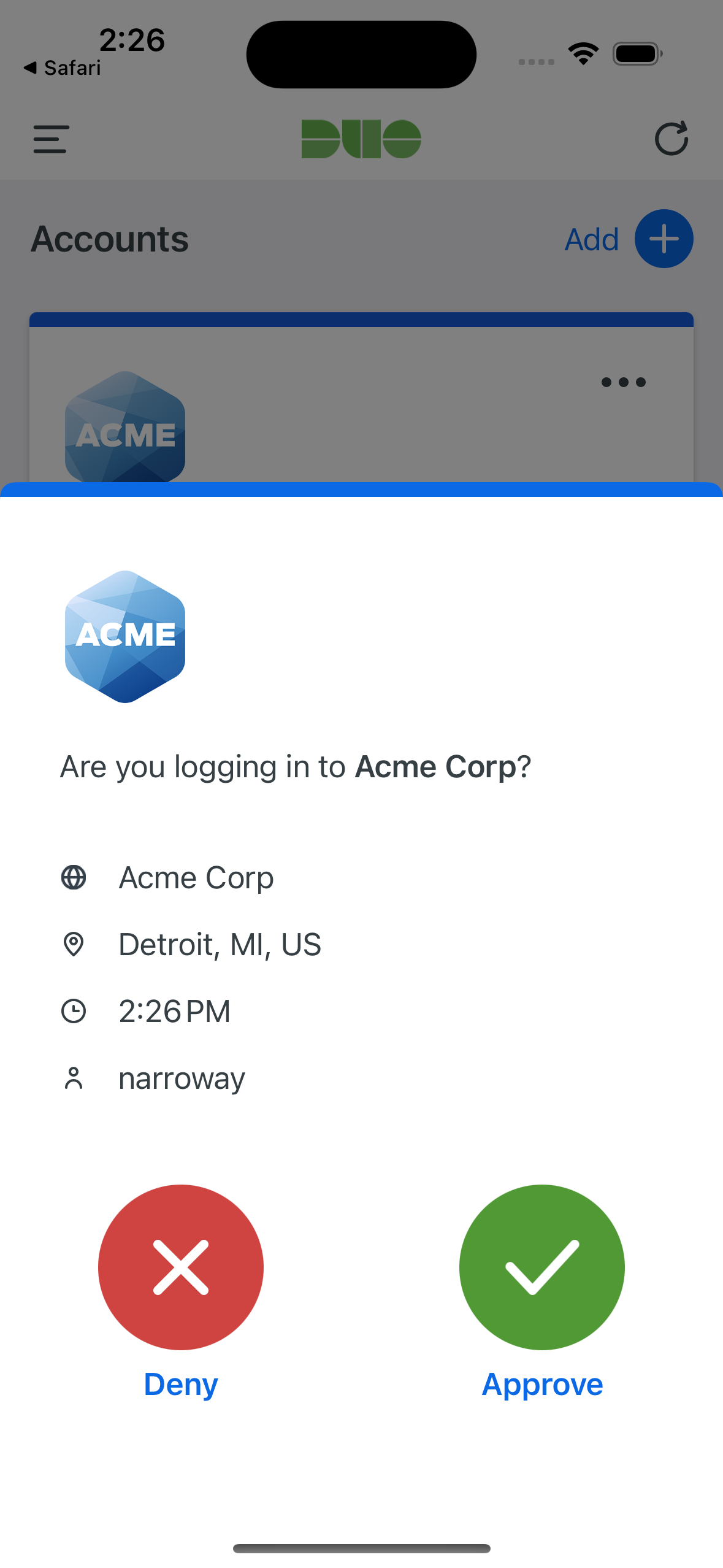
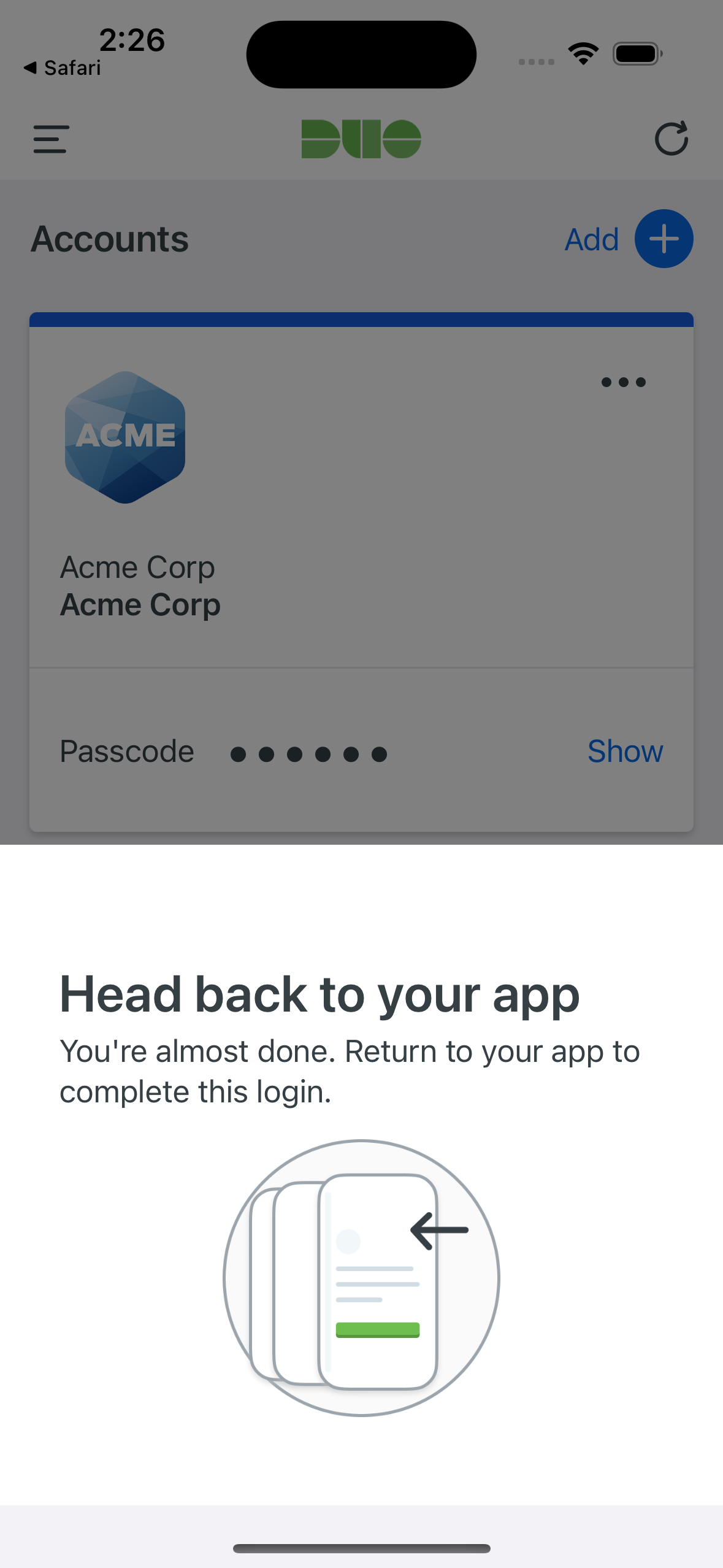
On Android devices, approving the request grants access and returns the user to the protected application. On iOS devices, after approving the Duo authentication request users tap the top-left of the Duo Mobile app to return to the application and complete login.
If the user does not have Duo Mobile activated for push, or does not approve the Duo request before it times out, the user returns to the Duo Prompt, where they may select from the available factors to complete 2FA.
Removing the Sophos Mobile Management Integration
Be sure to unassign your trusted endpoints policy from all applications or remove the "Trusted Endpoints" configuration item from your global policy before deleting an existing Sophos Mobile integration from "Trusted Endpoints Configuration". You should also disable your Duo admin user in Sophos Mobile.
Leaving the policy settings in place after deleting a management tools integration may inadvertently block user access to applications.
Deleting a trusted endpoints management tool integration from the Duo Admin Panel immediately invalidates issued Duo device authentication certificates.
Troubleshooting
Need some help? Take a look at our Trusted Endpoints Knowledge Base articles or Community discussions. For further assistance, contact Support.
